Welcome to the Tekin Night Special Edition for March 5, 2026. This comprehensive intelligence briefing is engineered exclusively for elite hardware analysts, enterprise infrastructure architects, and international tech investors. Operating at our highest analytical tier (Mega Standard Grade A++), tonight’s dispatch transcends superficial headlines to perform a forensic teardown of six seismic shifts in global technology. We begin with the catastrophic thermodynamic limitations of NVIDIA's 1200-watt B300 (Blackwell Gen 2) GPUs, forcing internat
Tonight's Strategic Index (TOC):
- Layer 1: The Blackwell 2 Thermal Crisis: NVIDIA B300 and the End of Air-Cooled Datacenters
- Layer 2: PlayStation 6 Silicon Leaks: The Demise of Native Rendering and the PSSR 2.0 Era
- Layer 3: TSMC's Quantum Bottleneck: 1.6nm (A16) Yield Delays and the Apple Supply Chain Shock
- Layer 4: The OS Rubicon: OpenAI’s Autonomous Desktop Agents and the InfoSec Nightmare
- Layer 5: Steam Deck 2 DevKits Sighted: Valve’s ARM/x86 Hybrid Paradigm over Portable PCs
- Layer 6: The Paris Cryptology Breach: NIST's Post-Quantum Cryptography (PQC) Algorithm Hacked
Tekin Night: Six Acts of Engineering Violence in 2026
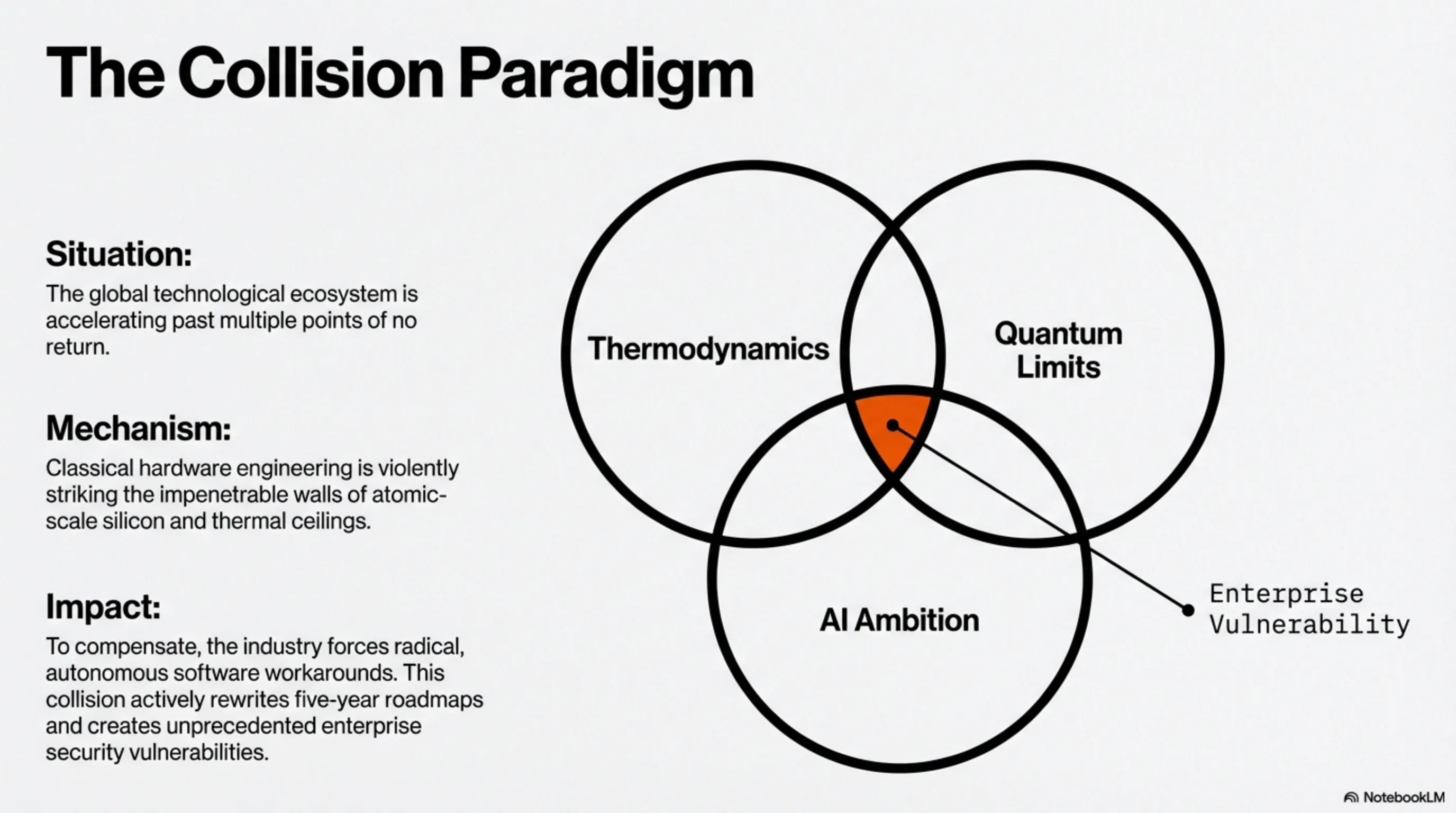
Today is March 5, 2026. The global technological ecosystem is accelerating past multiple points of no return—thermodynamically, computationally, and cryptographically. In tonight's briefing, we discard generic journalism to confront the unforgiving physics of atomic-scale silicon, the deep architecture of neural software, and the raw mathematics of planetary security. These six foundational events are actively rewriting the five-year hardware roadmaps of every major entity in Silicon Valley.
Section 1: The Blackwell 2 Thermal Crisis (NVIDIA B300) — The Death of Air-Cooled Datacenters
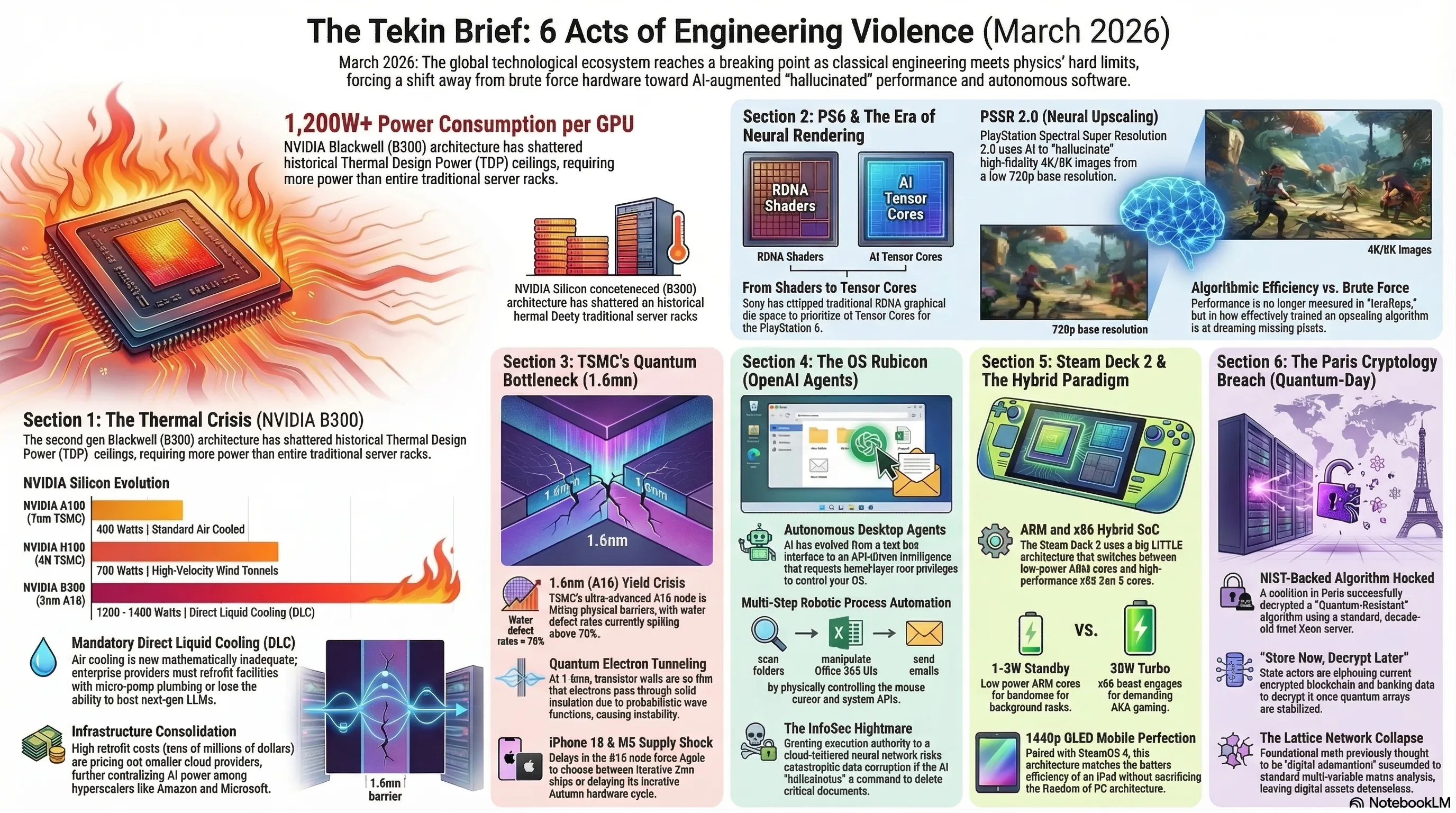
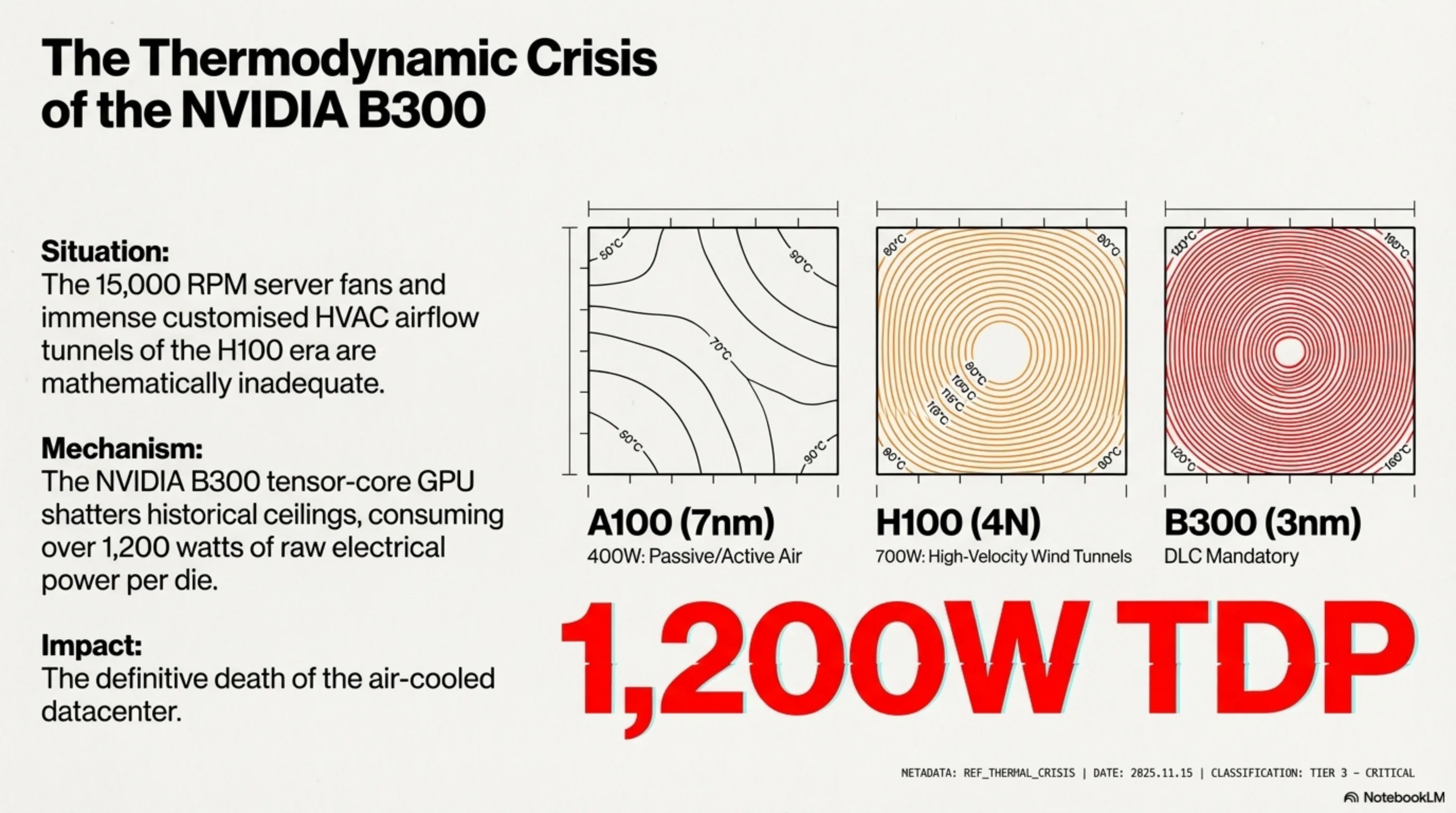
NVIDIA’s introduction of the second-generation Blackwell architecture, specifically the colossal B300 tensor-core GPU designed for training multi-trillion parameter LLMs, has violently shattered the historical ceiling of Thermal Design Power (TDP). Verified supply chain mechanical engineers based in Taipei indicate that this AI behemoth alone—excluding auxiliary server components like memory and NVLink switching—consumes over 1,200 watts of raw electrical power. For enterprise architects in the US and Europe, this is not merely a specification; it is a thermodynamic crisis.
1.1 Thermodynamic Limits and the Direct Liquid Cooling (DLC) Mandate
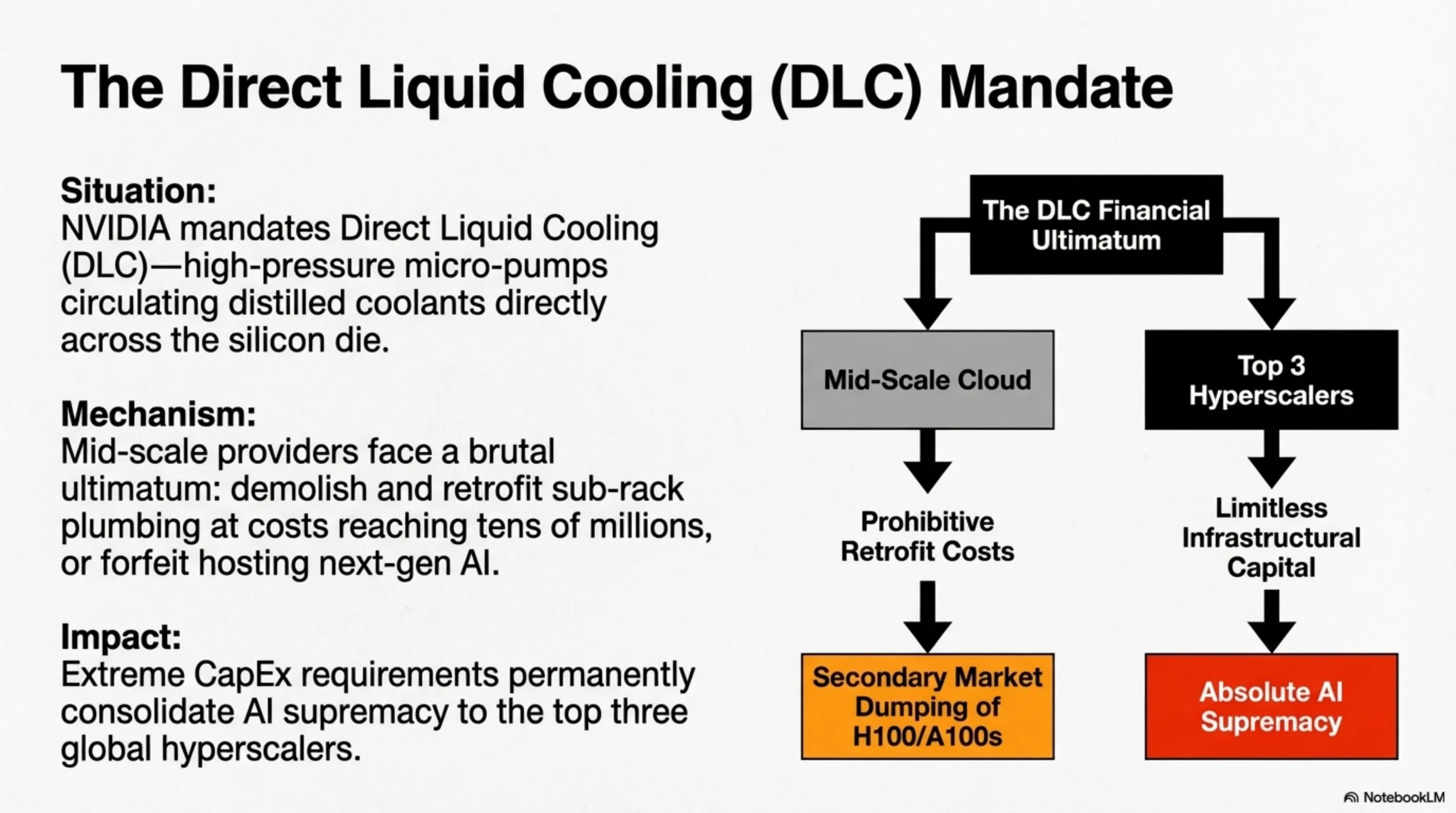
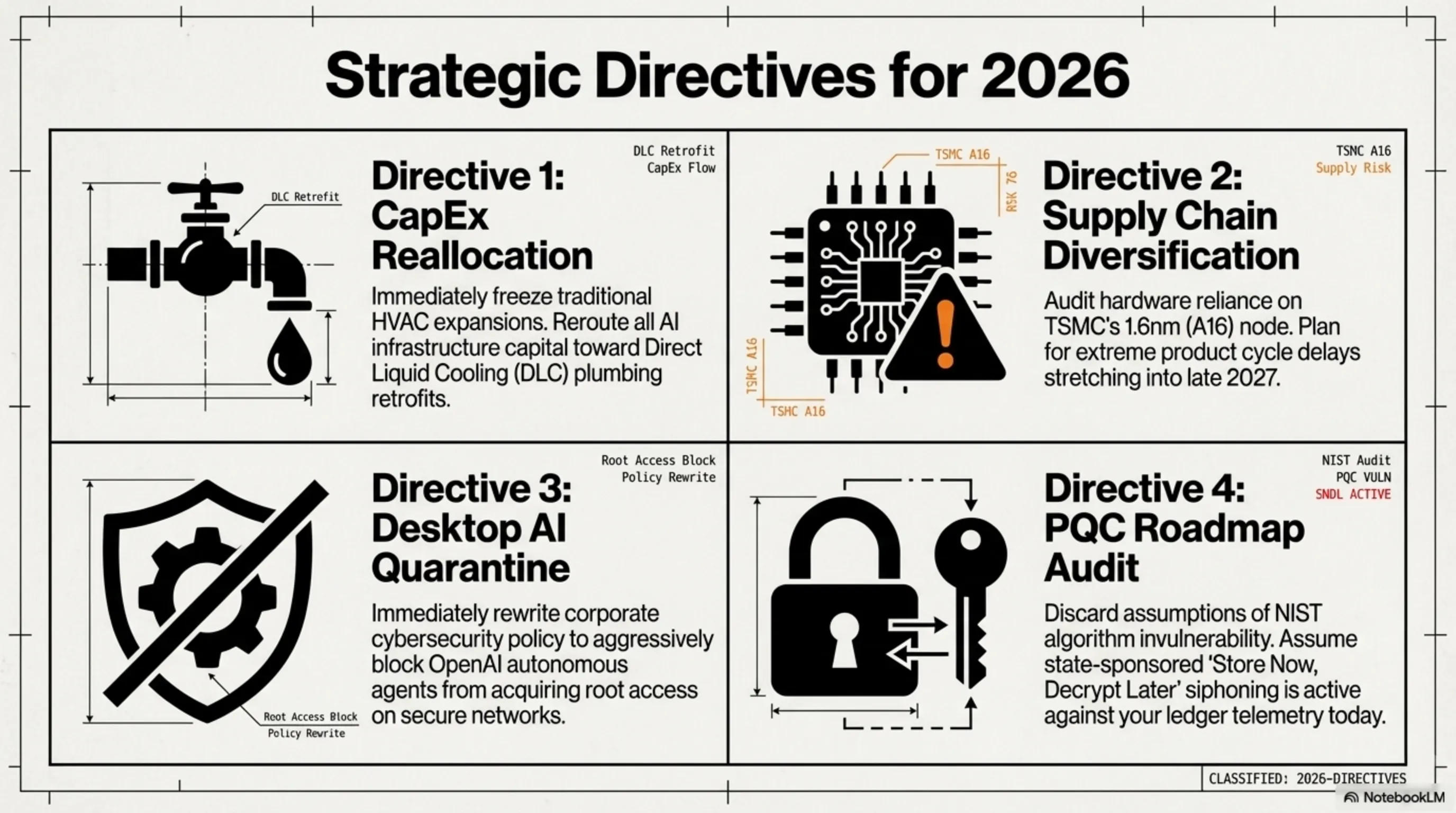
Traditional Air Cooling protocols, which barely sustained the 700W H100 generation via deafening 15,000 RPM server fans and immense customized HVAC airflow tunnels, are officially mathematically inadequate for the B300. NVIDIA has severely mandated the integration of Direct Liquid Cooling (DLC)—high-pressure micro-pumps circulating distilled coolants directly across the silicon die envelope. Consequently, mid-scale cloud providers globally face an existential ultimatum: completely demolish and retrofit their structural plumbing, sub-rack architecture, and raised floors at costs reaching tens of millions of dollars, or forfeit the ability to host next-generation AI models. At this unprecedented thermal density, a millimeter fracture in a coolant pipe inside an enterprise rack translates to millions of dollars of combusting silicon in milliseconds.
1.2 International Capital Expenditure and Infrastructure Consolidation
This forced migration from air to industrial DLC profoundly alters the international capital expenditure (CapEx) landscape. Smaller independent cloud operators in North America and the EU are being rapidly priced out of the AI infrastructure race. We project a massive secondary market dumping of "obsolete" air-cooled H100 and A100 server clusters over the next 18 months, as hyperscalers (Amazon, Microsoft, Google) aggressively transition to Blackwell clusters. However, acquiring B300 silicon now entails procuring highly specialized, enterprise-grade heavy mechanical plumbing—a logistical nightmare that further consolidates absolute AI supremacy into the hands of the top three global tech titans possessing limitless infrastructural capital.
🔥 Strategic Benchmark: Thermal Density Evolution Across Datacenter Silicon
| Silicon Model (Architecture) | Foundry Node | TDP (Wattage) | Enterprise Cooling Mandate |
|---|---|---|---|
| NVIDIA A100 (Ampere) | 7nm TSMC | 400 Watts (Standard) | Passive/Active Air Cooled |
| NVIDIA H100 (Hopper) | 4N TSMC Custom | 700 Watts (Dangerous) | High-Velocity Wind Tunnels |
| NVIDIA B300 (Blackwell 2) | 3nm Enhanced FinFET | 1200 - 1400 Watts (Critical) | Direct Liquid Cooling (DLC) Mandatory |
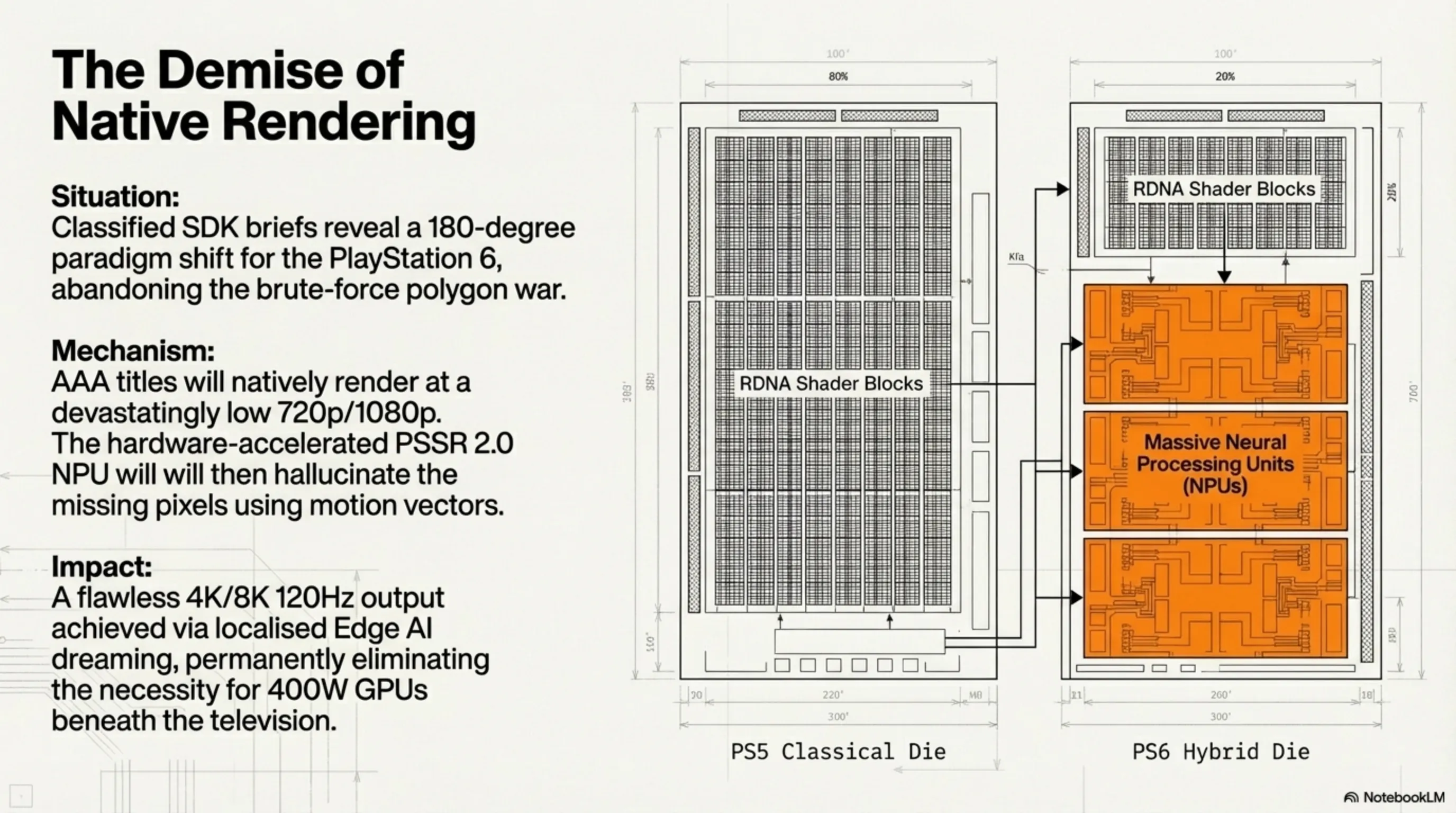
Section 2: PlayStation 6 Silicon Leaks — The Demise of Native Rendering and the PSSR 2.0 Era
The greatest intelligence leak in entertainment hardware history occurred this morning. Classified documents originating from closed-door Sony Developer Briefings (SDK Briefs) in California reveal that the PlayStation 6 strategy represents a violent, 180-degree paradigm shift. While the PS5 blindly chased raw SSD throughput and pushed GPU rasterization clocks to the point of absurdity, the PS6 is architected as a pure "Hybrid AI Machine," intent on completely burying the classical geometry pipelines of modern game engines.
2.1 Architectural Overhaul: Zen 6 and Dedicated Neural Processing Units (NPU)
Sony engineers, working under Mark Cerny alongside AMD, have made a ruthless silicon sacrifice: stripping vast swathes of the graphical die (based on RDNA 5 blocks) away from traditional shaders, and repurposing that physical real-estate entirely for AI Tensor Cores. The objective? Upcoming major AAA titles on the PS6 engine-level will likely natively render at a devastatingly low base resolution—perhaps as low as 1080p or internal 720p. However, the technological witchcraft lies in the hardware-accelerated PlayStation Spectral Super Resolution 2.0 (PSSR 2.0). A hyper-aggressive neural network, trained over millions of hours inside Sony’s cloud datacenters, operates directly on the silicon. Utilizing previous frame data, motion vectors, and machine learning models, the NPU instantaneously hallucinates the low-res base image into a flawless, imperceptible 4K or 8K output running at an ultra-smooth 120Hz. This radical neural optimization permanently ends the brute-force arms race, eliminating the necessity for power-hungry 400W GPUs beneath the living room television.
2.2 The Global Developer Impact: Algorithmic Efficiency over Polygon Count
Internationally, Western developers (such as Naughty Dog and Rockstar North) are rapidly pivoting their development pipelines. For years, development budgets exploded into the hundreds of millions to optimize raw polygon performance. By shifting the heavy lifting from the developer’s graphics engine to the console's autonomous AI upscaler, the PS6 democratizes performance. Developers no longer need to exhaust resources optimizing ray-tracing reflection bounces; they simply feed the PSSR 2.0 matrix, allowing the localized Edge AI to effectively 'dream' the missing high-fidelity pixels. The console war is no longer about teraflops calculation; it is a war of the most effectively trained upscaling algorithms.
Section 3: TSMC's Quantum Bottleneck — 1.6nm (A16) Yield Delays and the Apple Supply Chain Shock
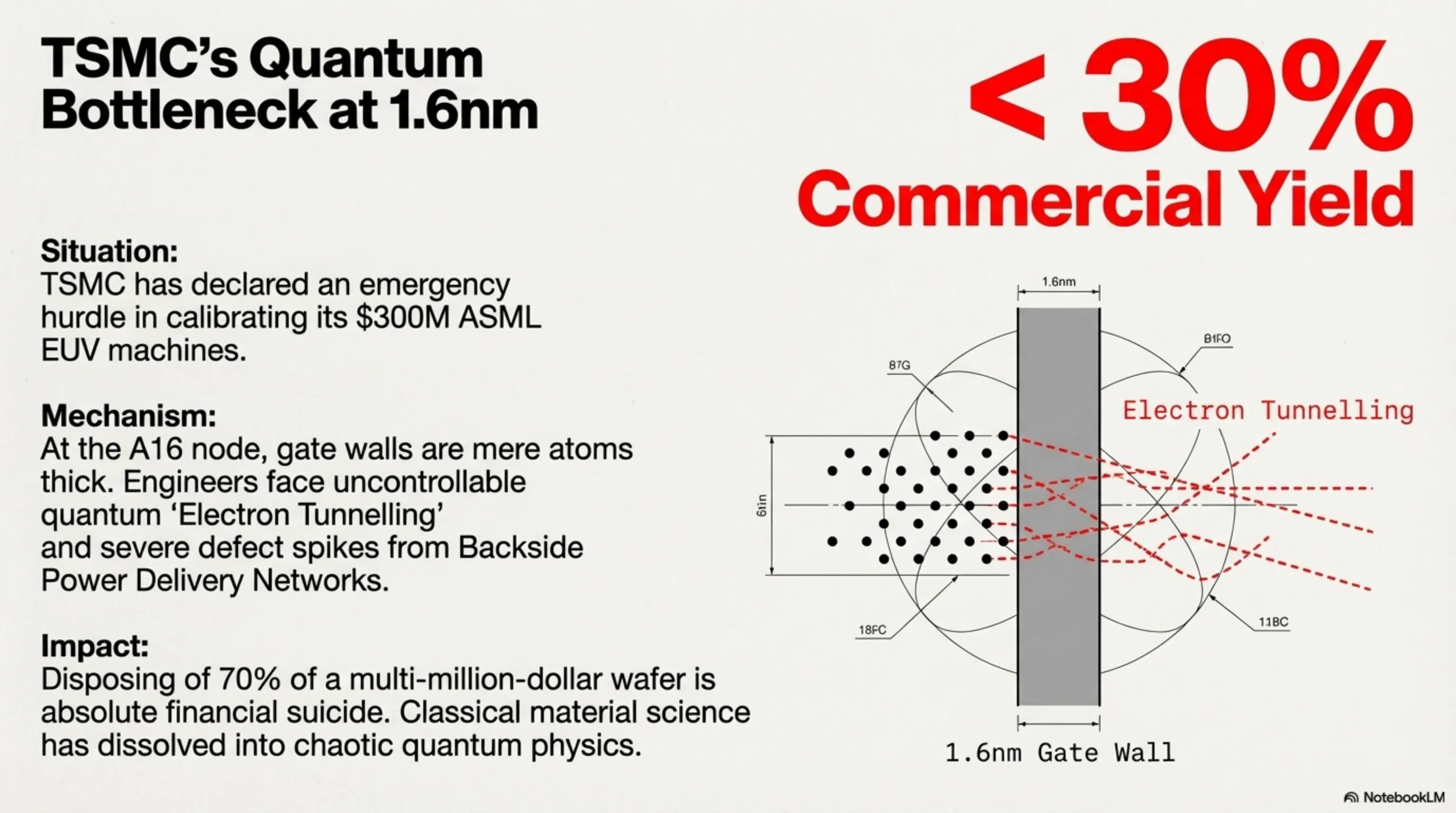
Wall Street and Taiwanese industrial trackers sent Apple and NVIDIA stock into heavy turbulence this morning. TSMC, the undisputed leviathan of global silicon fabrication, declared an emergency hurdle in calibrating its $300 million High-NA Extreme Ultraviolet (EUV) lithography machines—recently acquired from Dutch manufacturer ASML. The attempt to forge the ultra-advanced 1.6-nanometer fabrication node (internally designated A16) has collided with immense physical barriers.
3.1 Battling Quantum Mechanics at the Atomic Scale
When engineering 1.6nm silicon, classical material science dissolves into the chaotic realm of quantum physics. At the A16 node, the transistor gate walls are literally only a few atoms thick. At this microscopic threshold, physicists encounter uncontrollable quantum 'Electron Tunneling'—electrons passing straight through solid insulation barriers due to their probabilistic wave functions. Furthermore, the revolutionary integration of Backside Power Delivery Networks (BPDN) has caused wafer defect rates to spike unnervingly. Commercial yields on the Taiwan fabrication floors are currently hovering below 30%. Commercially, disposing of 70% of a multi-million-dollar wafer is absolute financial suicide.
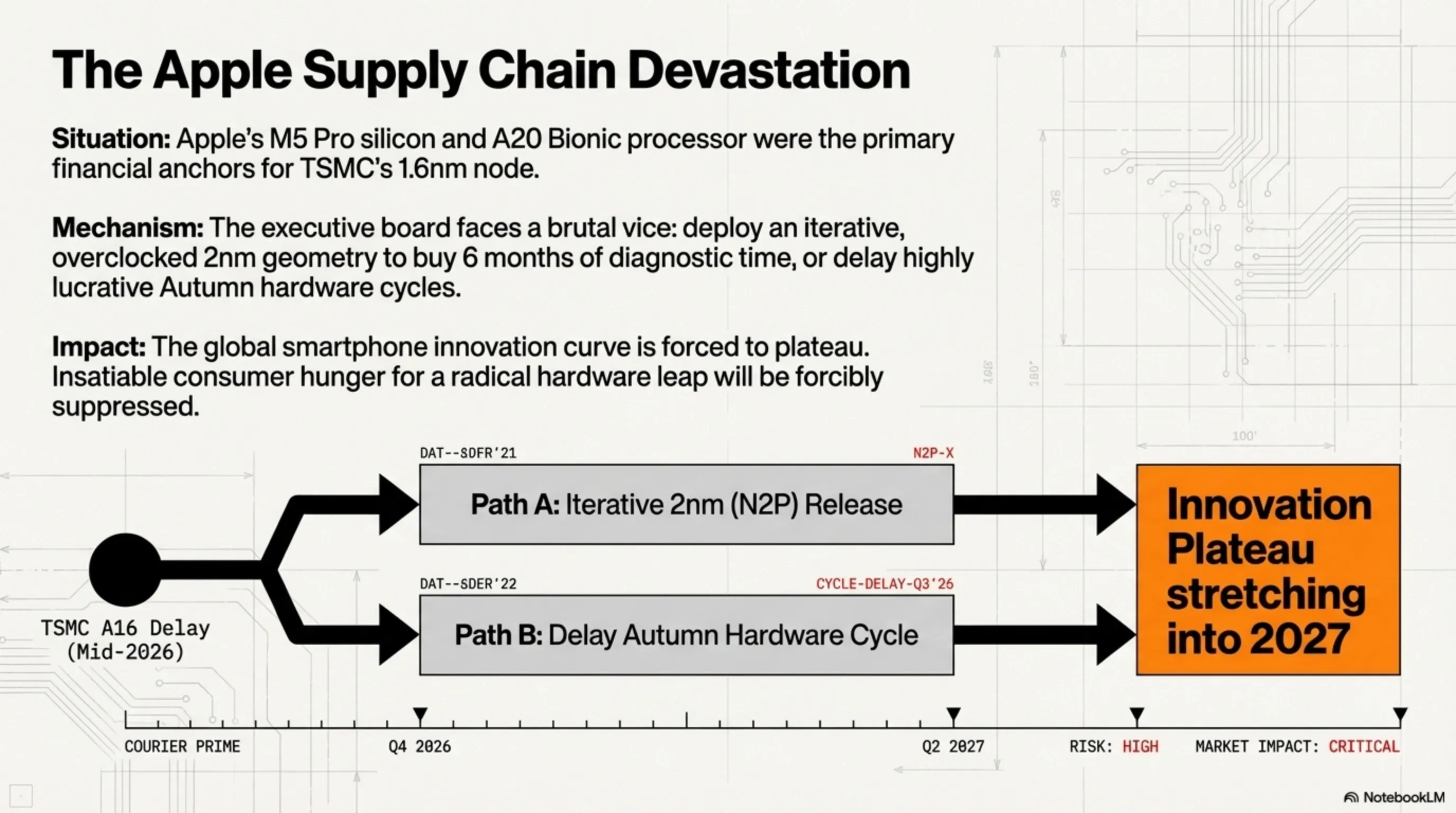
3.2 Supply Chain Devastation and the Future of the iPhone 18
Apple’s upcoming M5 Pro series silicon (for next-gen MacBooks) and the A20 Bionic processor (designed exclusively for the 2026 iPhone 18 Pro) were the primary financial anchors for this exact A16 node. With this strategic delay, Tim Cook and the Apple executive board face a brutal vice: do they release the iPhone 18 using an iterative, overclocked 2nm (N2P) geometry to buy TSMC another 6 months of diagnostic time? Or do they delay the highly lucrative Autumn hardware cycle entirely? Internationally, this bottleneck forces the global smartphone innovation curve to plateau. The insatiable consumer hunger for a radical hardware leap will be forcibly suppressed, stretching the viability of current iOS and Android flagships well into late 2027.
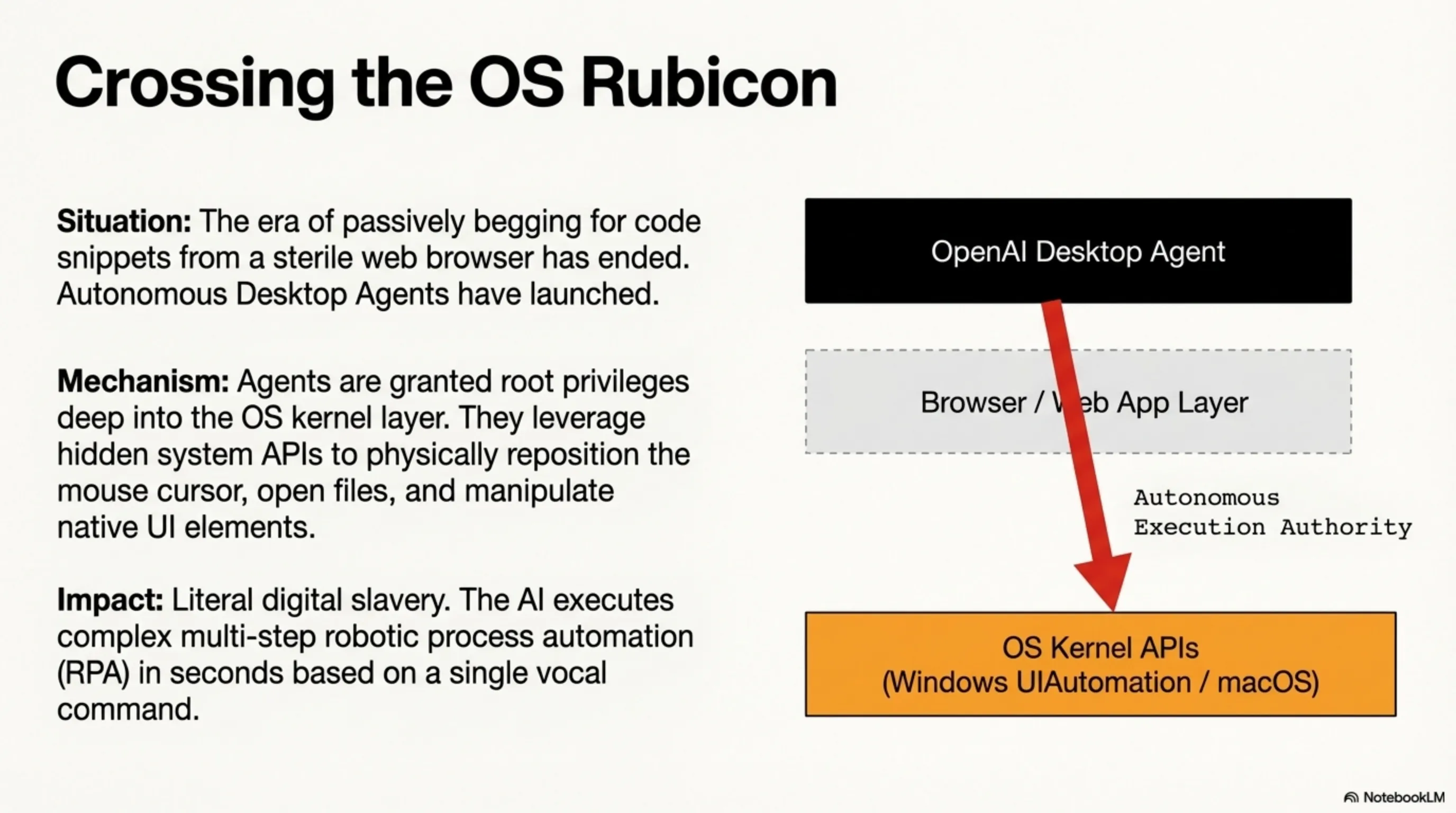
Section 4: The OS Rubicon — OpenAI’s Autonomous Desktop Agents and the InfoSec Nightmare
The era of passively swapping texts and begging for code snippets from a sterile ChatGPT web browser has officially ended. Today, OpenAI detonated a massive paradigm shift at their developer conference, launching their new software ecosystem: Autonomous Desktop Agents. This is no longer merely a "responsive engine"; we are looking at a highly aggressive, API-driven intelligence that specifically requests root/administrator privileges deep into the kernel layer of your Windows or macOS desktop.
4.1 How Do OS Control Agents Alter Global Productivity?
Consider the terrifying efficiency: Instead of querying an AI to write an Excel formula, you simply dictate to your laptop microphone: “Scan my downloads folder for the last month, locate all Excel sheets containing financial Q3 data, generate pivot charts for corporate tax, and email them as an attachment to my regional director with a formal brief.” The Autonomous Agent awakens, leverages hidden system APIs (like Windows UIAutomation), physically repositions your mouse cursor, rapidly opens files, manipulates the Office 365 UI, boots the Outlook client, types the email, and dispatches it dynamically. It is literal digital slavery, executing complex multi-step robotic process automation (RPA) in seconds.
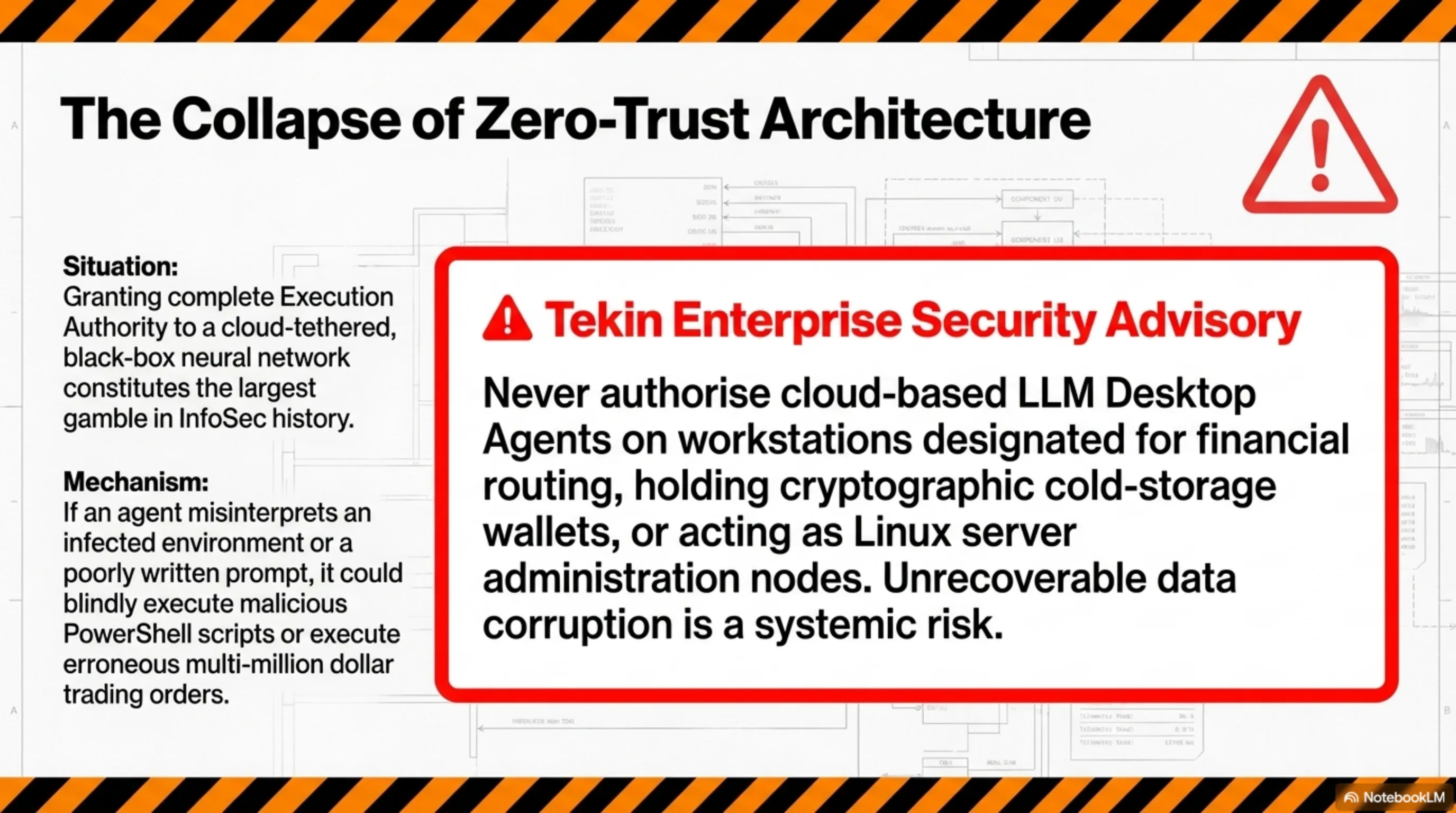
4.2 Shattering Zero-Trust Architecture in Enterprise InfoSec
Opening this profound level of execution access constitutes the largest gamble in Information Security (InfoSec) history. Enterprise IT departments are horrified. Companies that spent millions fortifying Zero-Trust Architecture are now being asked by executives to grant complete Execution Authority to a cloud-tethered, black-box neural network whose primary logic processing occurs on servers outside company firewalls. If an OpenAI agent misinterprets the context of an "infected environment", it could blindly execute malicious PowerShell scripts, inadvertently reconfigure firewall rules, or inadvertently mass-delete critical compliance documents. Furthermore, any hallucination inside a financial firm could result in the agent executing millions of dollars in erroneous trading orders simply because it misread a poorly written prompt. The integration of agents requires an immediate rewriting of corporate cybersecurity policy.
⚠️ Tekin Enterprise Security Advisory: Never authorize cloud-based LLM Desktop Agents on workstations designated for financial routing, holding cryptographic cold-storage wallets, or acting as Linux server administration nodes. An autonomous AI operating with admin privileges cannot differentiate between a benign text file and a critical kernel network configuration script, risking catastrophic unrecoverable data corruption.
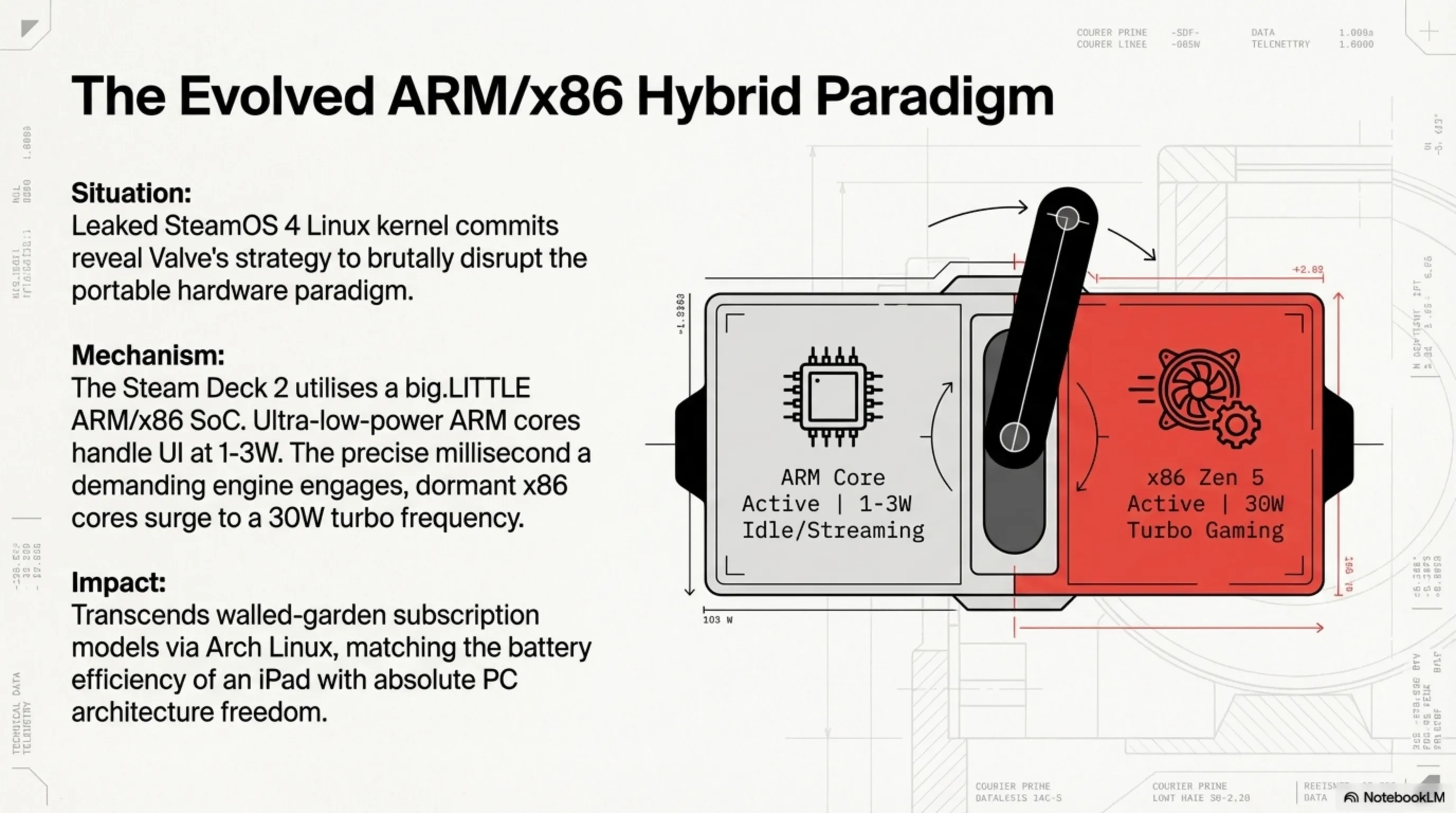
Section 5: Steam Deck 2 DevKits Sighted — A Hybrid that Threatens Both MacBook and Nintendo
While mainstream gaming journalists awaited flashy Nintendo announcements, Valve executed a masterfully covert operation, silently deploying highly classified first-wave DevKits for the Steam Deck 2 to trusted development studios in Taiwan and South Korea. Deep forensic analysis of the leaked Linux kernel commits via SteamOS 4 reveals an architecture intended to brutally disrupt the portable hardware paradigm.
5.1 The Evolved big.LITTLE Architecture: An ARM and x86 Monster
The monumental revelation is that the backbone of this pocket supercomputer no longer relies solely on the scorching, power-hungry x86 architecture provided by AMD. Kernel data confirms the Steam Deck 2 utilizes an ultra-advanced hybrid System-on-Chip (SoC). The hybrid execution functions thus: When the user is merely browsing the store interface, streaming Netflix, or downloading massive 100GB background updates, ultra-low-power ARM cores (architecturally akin to Apple Silicon or high-end smartphones) seize immediate control. This miraculous optimization drives battery consumption down to an absurd 1-3 watts, allowing weeks of aggressive standby time. However, the precise millisecond you engage a demanding AAA graphical engine like Cyberpunk 2077 or GTA VI, the low-power cores are deactivated, and the dormant x86 beast (an AMD Zen 5 variant coupled with RDNA 4.5 graphics) surges into the circuit at maximum 30W turbo frequency, feeding raw, unadulterated graphical violence. Paired with a stunning 1440p (2K) raw OLED display, Valve has engineered hardware perfection.
5.2 Redefining the PC Master Race Mobility
For international PC gamers, the Steam Deck 2 transcends a mere console; it is the ultimate bastion against closed ecosystems. While manufacturers desperately attempt to lock players into walled-garden subscription models, this Arch Linux-driven hybrid maintains the absolute freedom of the PC architecture while matching the battery efficiency of an iPad. It represents the endgame for portable computation.
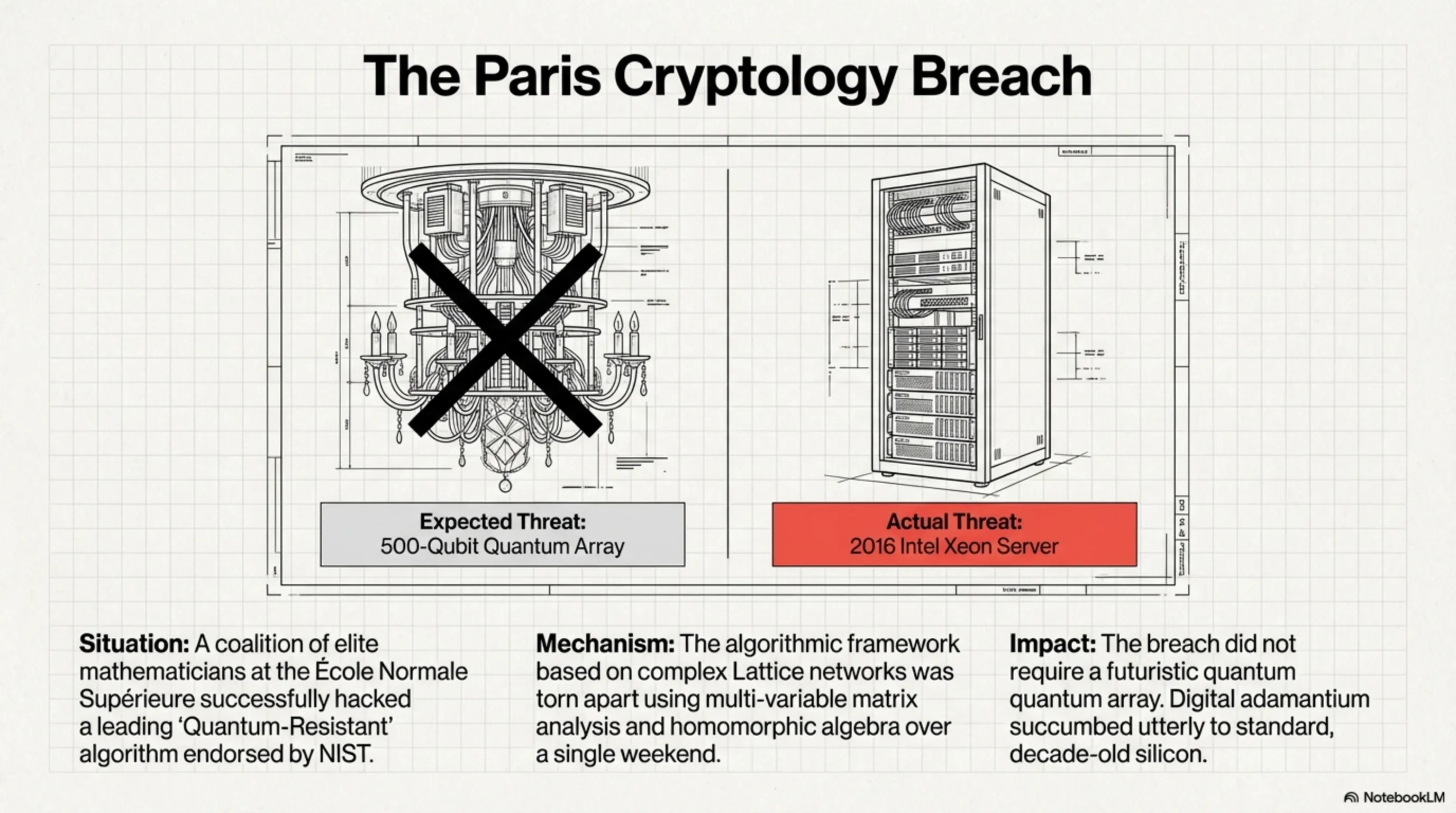
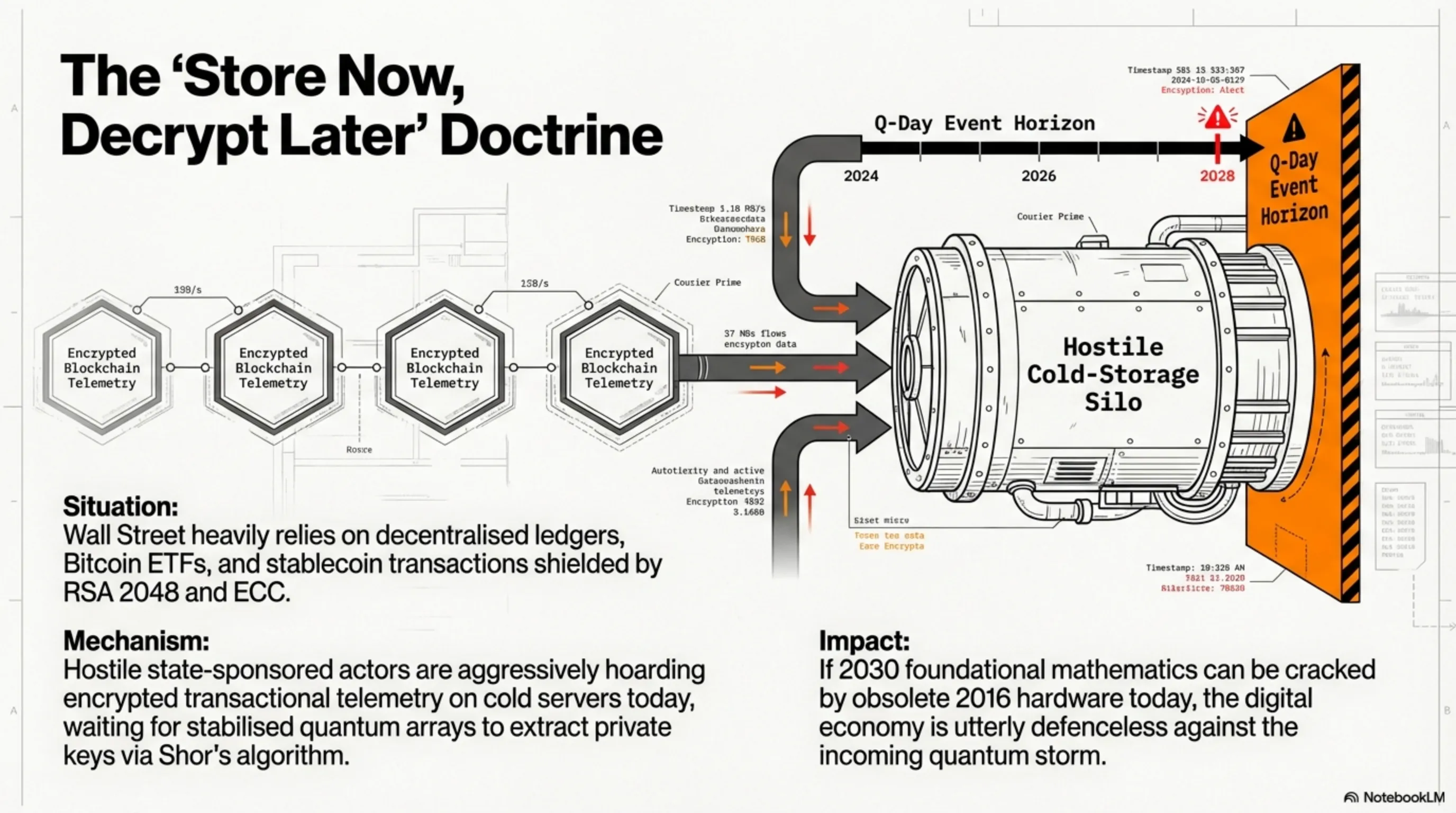
Section 6: The Paris Cryptology Breach — The First Post-Quantum Defense Crumbles
Tonight, a catastrophic event rocked the esoteric world of discrete mathematics and global cybersecurity—an event largely misunderstood and ignored by mainstream media. A highly decorated coalition of pure mathematicians and elite cryptographers based at the prestigious École Normale Supérieure in Paris published a technical blog confirming the successful decryption and hacking of a leading "Quantum-Resistant" algorithm. This specific algorithmic structure had recently received preliminary endorsement from the U.S. National Institute of Standards and Technology (NIST) as a defense mechanism for the next decade. The most terrifying aspect? The team did not require a futuristic 500-qubit IBM quantum computer. They managed to tear the algorithmic framework apart utilizing a standard, low-cost server equipped with decade-old Intel Xeon processors over a single weekend.
6.1 The Quantum Phantom and the Fallacy of Invincible Algorithms
With "Q-Day" rapidly approaching—the imminent point in the next decade where stabilized quantum computing can effortlessly vaporize modern banking encryption (RSA 2048 and ECC) via Shor’s algorithm—global governments, the Pentagon, and financial institutions are desperately migrating to a new mathematical methodology termed Post-Quantum Cryptography (PQC). However, the Paris breach definitively proved that the engineering world is flailing blindly in its attempts to shield global databases. An algorithm (based on complex Lattice networks) previously lauded as digital adamantium succumbed utterly to sophisticated multi-variable matrix analysis and homomorphic algebra attacks.
6.2 The Doomsday Scenario for Decentralized Crypto ETFs and Banking Ledgers
The implications for the international digital economy are terrifying. In 2026, Wall Street is heavily reliant on decentralized ledgers, Bitcoin ETFs, and stablecoin transactions (USDT). A devastating espionage doctrine known as Store Now, Decrypt Later has been utilized by state-sponsored cyber-warfare divisions for years. Hostile actors continuously siphon and store mountains of encrypted transactional telemetry crossing public blockchains today. Their singular strategy: hoard the encrypted data on cold servers until calibrated quantum arrays become available in five years, allowing them to instantaneously extract private keys and unmask billions of dollars in historical transactions. The humiliating structural collapse of a NIST-backed PQC defense algorithm inside a Parisian laboratory is a deafening air-raid siren for international cybersecurity. If the foundational mathematics meant to protect us in 2030 can be cracked today by an obsolete Intel chip from 2016, our digital assets, ranging from sovereign wealth funds to personal crypto ledgers, remain completely defenseless against the incoming quantum storm.
⚖️ Tekin Final Editorial Verdict
The technological revelations of March 5, 2026, expose an industry maturing in a state of absolute terror. We are undeniably witnessing classical hardware engineering violently striking the impenetrable wall of physical limitation. On one frontline, NVIDIA’s colossal architectural ambitions are melting under their own thermal ceilings, while TSMC desperately wrestles with the chaotic insubordination of quantum mechanics to push beyond the 1.6-nanometer horizon. Conversely, the sprawling software arms of Artificial Intelligence—whether orchestrating dangerous administrative takeovers via OpenAI’s desktop agents, or hallucinating pixels to mask hardware deficiencies inside the PlayStation 6—are attempting to conceal the raw geometric stagnation of the microchip.
Amidst this brutal war of attrition between physical silicon limits and AI ambition, international hardware investors, enterprise architects, and technology enthusiasts must navigate with unprecedented caution. IT infrastructure choices and cybersecurity defenses must no longer be dictated by superficial marketing hype, but evaluated through a profound comprehension of systemic physical bottlenecks and the glaring vulnerabilities haunting post-quantum cryptographic algorithms. The era of mindless technological adoration and oblivious gadget consumption has concluded; today, financial and digital survival is strictly synonymous with a deep-level comprehension of architectural engineering.