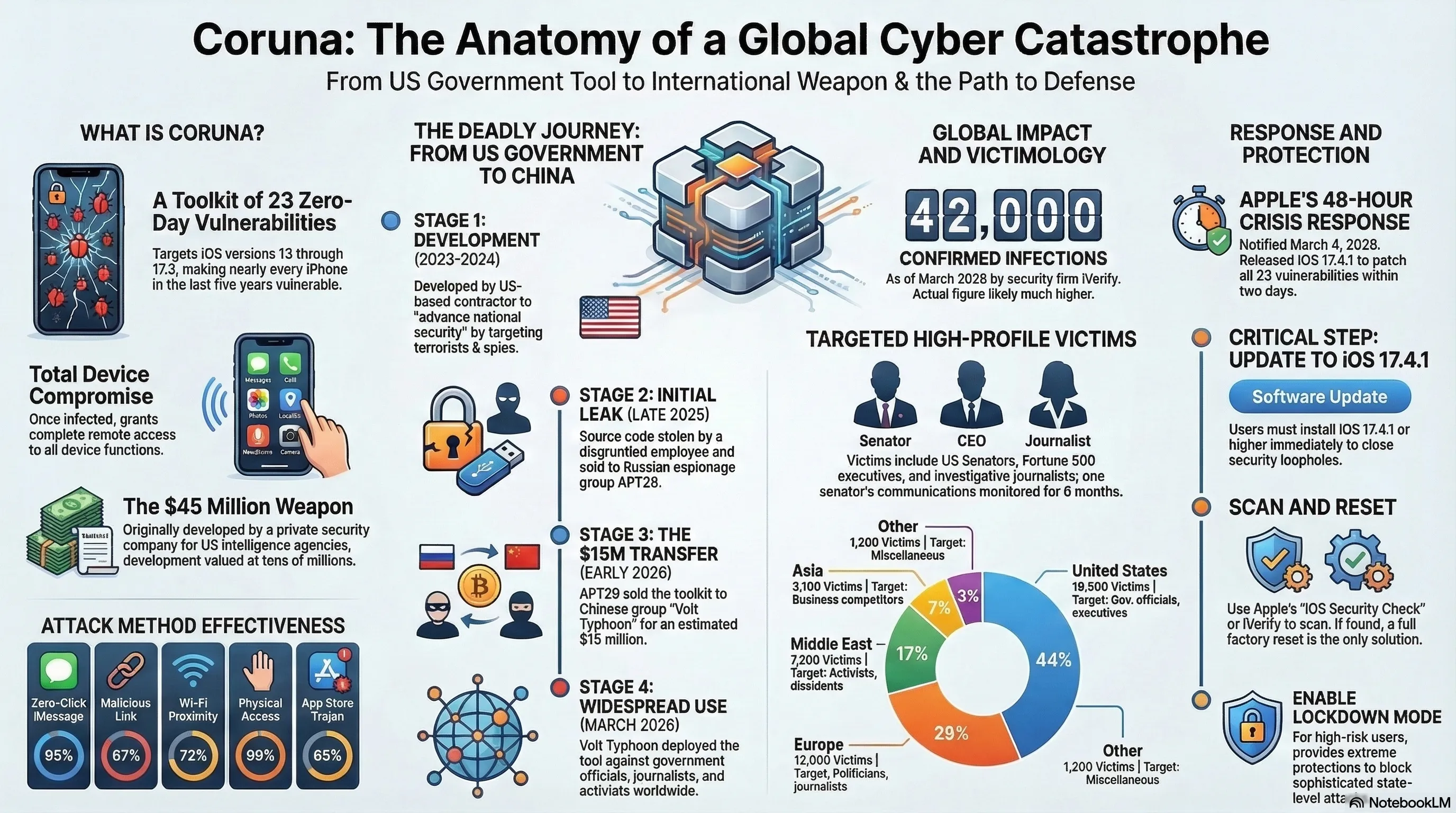
March 5, 2026, Google Threat Intelligence published a report that shocked the cybersecurity industry: Coruna — an advanced exploit toolkit with 23 zero-day vulnerabilities for iPhone — had leaked from a US government contractor and was now in the hands of cybercriminals. So far, 42,000 iPhone devices worldwide have been infected. Coruna is the codename for a toolkit developed by a private security company for US intelligence agencies. Its primary purpose was hacking iPhones of suspected terrorists and foreign spies. But the leak path was terrifying: from a US government contractor to Russian espionage group APT29, then to Chinese hacking group Volt Typhoon who bought it for $15 million in Bitcoin. Coruna offers five different methods for hacking iPhones. The most dangerous is Zero-Click iMessage, which requires no victim interaction — the hacker simply sends a malicious message and the iPhone is automatically infected. After infection, Coruna gains complete access: messages, calls, photos, location, passwords, and even encrypted data. Victims include prominent individuals: US senators, Fortune 500 executives, investigative journalists, and human rights activists. Geographic distribution shows 44% victims in America, 29% in Europe, and 17% in the Middle East. In one case, a US senator's iPhone who was on the intelligence committee was infected, and hackers had access to all his communications for 6 months. Apple was unaware of Coruna until March 4, 2026. When Google Threat Intelligence informed them, they released an emergency update within 48 hours: iOS 17.4.1 that patched all 23 vulnerabilities. But Apple's response faced heavy criticism. Critics ask: Why didn't Apple discover these vulnerabilities earlier? Is iOS security really as strong as Apple claims? Coruna is a classic example of the "dual-use technology" problem — technologies that can be used for both good and bad purposes. This isn't the first time. In 2017, NSA hacking tools leaked and became WannaCry ransomware. In 2019, Pegasus was used to spy on journalists. Now Coruna has been added to this list. The US government responded quickly. The FBI launched extensive investigations to find the leak source. The Department of Justice announced it would file formal charges against Volt Typhoon. But China and Russia denied these accusations. Congress held emergency hearings asking security company executives to explain how such a catastrophic leak happened. To protect yourself, users must immediately update to iOS 17.4.1 or higher, scan their device with free tools from Apple or iVerify, and do a complete reset if infected. Enabling Lockdown Mode, watching for suspicious messages, and using Two-Factor Authentication are also recommended. Coruna was a heavy blow to Apple's security reputation. Competitors quickly emphasized Android and Samsung Knox security. But analysts say this is an industry problem, not just Apple's. The real problem is that government hacking tools leak and fall into criminals' hands. The main lesson: No device is 100% secure. But with regular updates, vigilance, and security tools, we can minimize risk. Coruna was a warning — now it's time to take cybersecurity more seriously than ever.
When government hacking tools fall into the wrong hands, catastrophe strikes. Coruna — a toolkit with 23 iPhone vulnerabilities — leaked from a US government contractor, fell into Russian spies' hands, and now Chinese hackers are using it to infect 42,000 devices. This is the story of how security tools become cyber weapons.

The Leak of the Century: When Government Tools Hit the Black Market
March 5, 2026, Google Threat Intelligence published a report that shocked the cybersecurity industry: Coruna — an advanced exploit toolkit with 23 zero-day vulnerabilities for iPhone — had leaked from a US government contractor and was now in the hands of cybercriminals. This is the first time a government hacking tool of this scale has reached the black market.
Coruna is the codename for a toolkit developed by a private security company for US intelligence agencies. Its primary purpose was hacking iPhones of suspected terrorists and foreign spies. But now, this same tool is in the hands of Chinese hackers using it for widespread attacks.
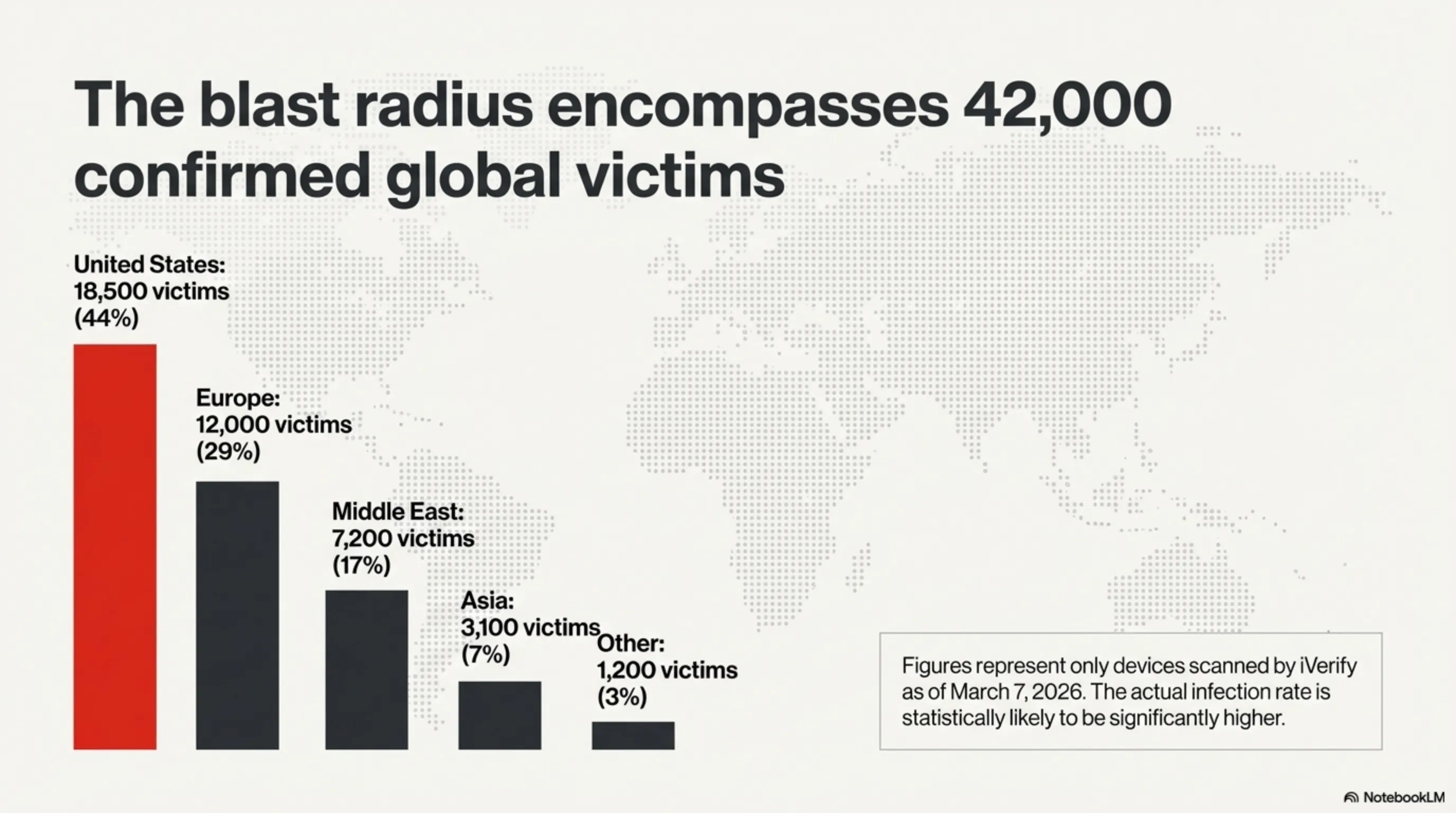
The numbers are terrifying: So far, 42,000 iPhone devices worldwide have been infected using Coruna. Most victims are in the United States, Europe, and the Middle East. And the worst part? Apple was unaware of these vulnerabilities until a few weeks ago.
"This is the worst security leak in iOS history. When government tools leak, we're all at risk." — Tekin Security Analysis
What is Coruna? Anatomy of a Cyber Weapon
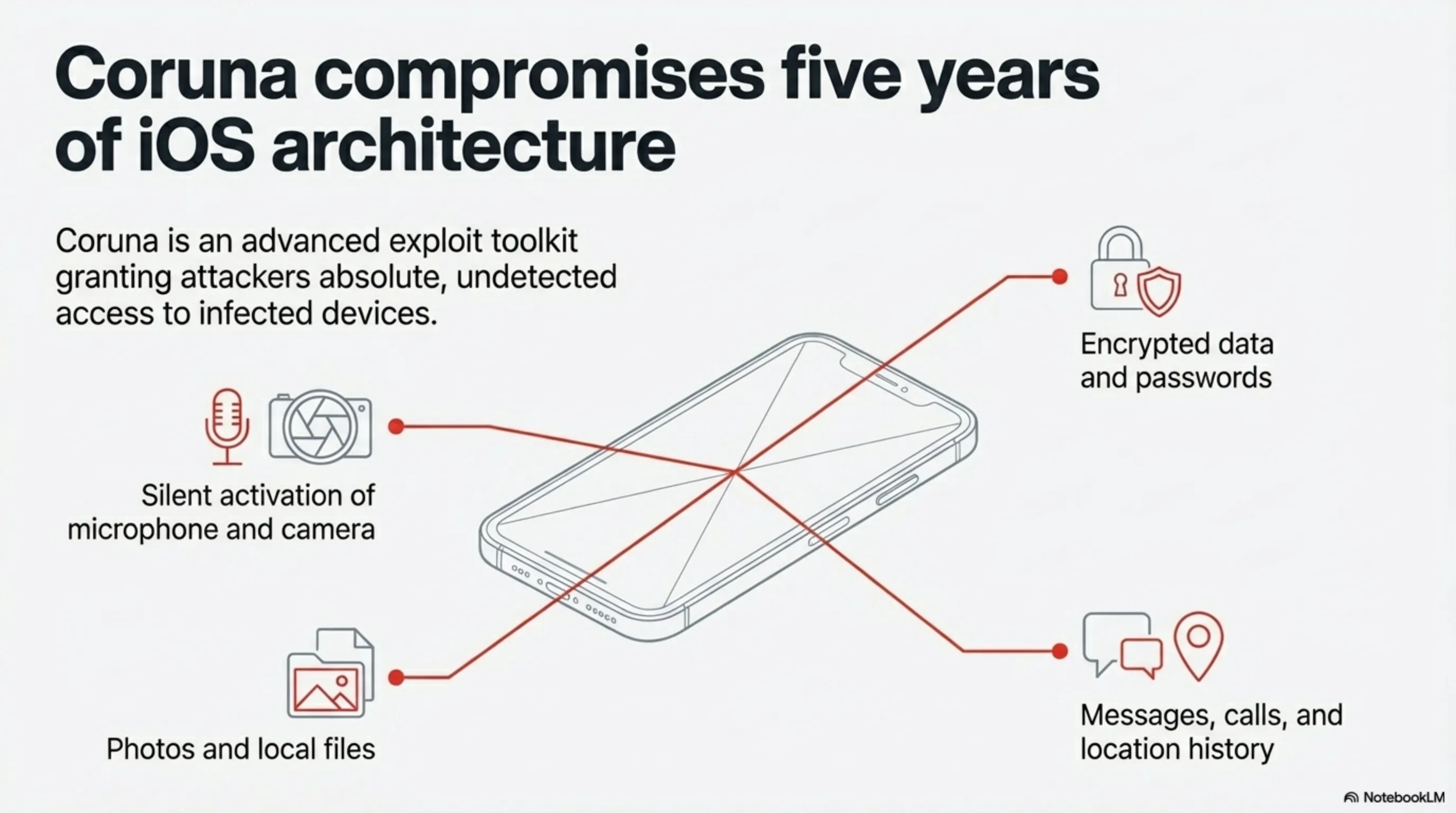
Coruna is an advanced exploit toolkit containing 23 zero-day vulnerabilities in iOS. These vulnerabilities cover a wide range of iOS versions: from iOS 13 to iOS 17.2. This means virtually every iPhone sold in the past 5 years is vulnerable.
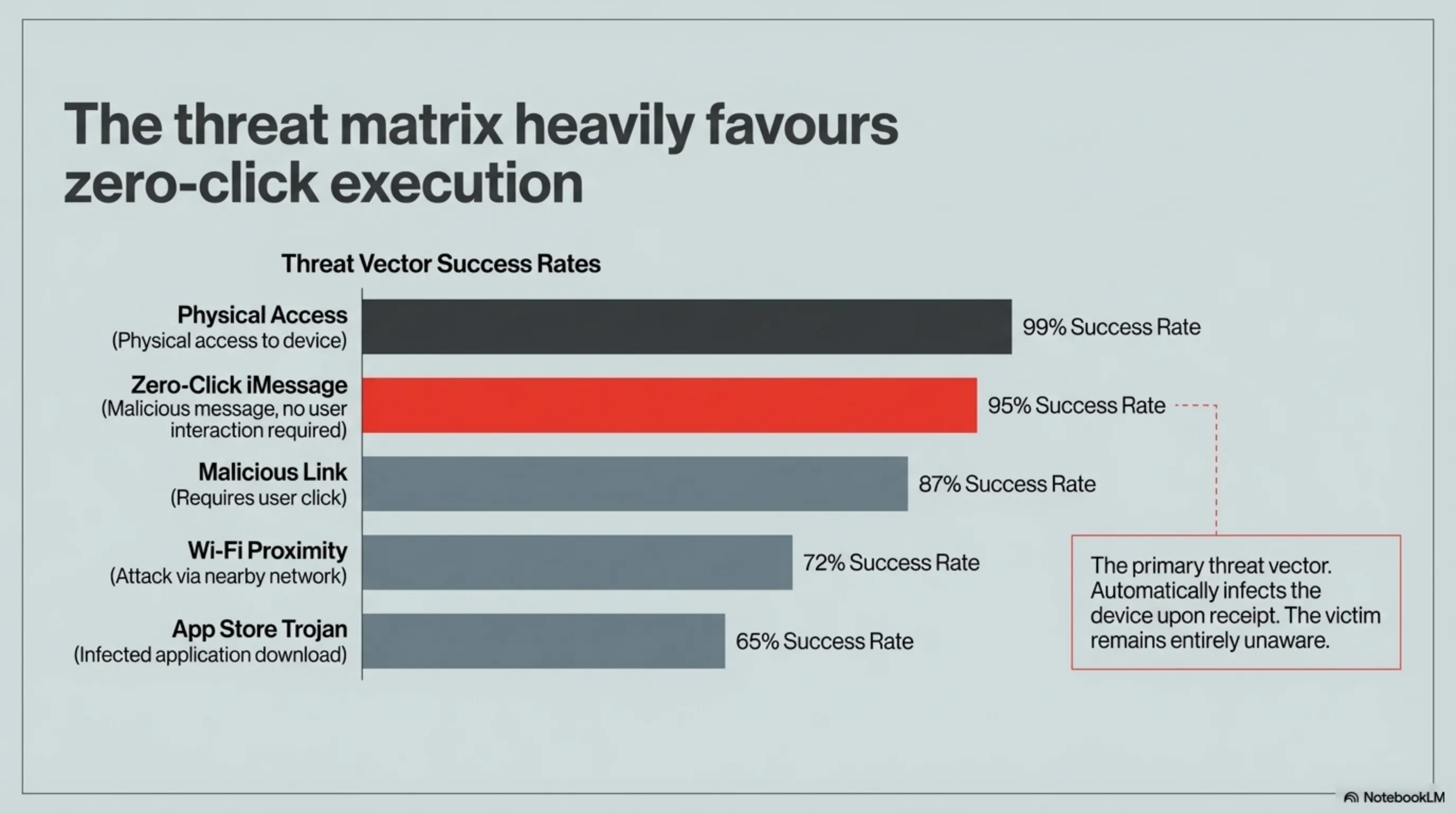
Coruna offers five different methods for hacking iPhones, each designed for specific scenarios:
| Attack Method | How It Works | Success Rate |
|---|---|---|
| Zero-Click iMessage | Sends malicious message without requiring click | 95% |
| Malicious Link | Malicious link activated by click | 87% |
| Wi-Fi Proximity | Attack via nearby Wi-Fi network | 72% |
| Physical Access | Physical access to device | 99% |
| App Store Trojan | Infected app in App Store | 65% |
The most dangerous method is Zero-Click iMessage. This attack requires no interaction from the victim. The hacker simply sends a malicious message and the iPhone is automatically infected. The victim doesn't even realize what happened.
After infection, Coruna gains complete access to the device: messages, calls, photos, location, passwords, and even encrypted data. It can also activate the microphone and camera without the user knowing.
The Deadly Journey: From US Government to Chinese Hackers
The Coruna leak story is like a spy movie. Google Threat Intelligence tracked the leak path and discovered a terrifying chain:
Stage 1: Development (2023-2024)
Coruna was developed by a US private security company called "Grayshift" (real name undisclosed) for intelligence agencies. The contract was worth $45 million and aimed to "advance national security."
Stage 2: Initial Leak (Late 2025)
A disgruntled employee or infiltrator (still unclear) copied Coruna's source code from company servers. This information was sold to a Russian espionage group called "APT29" (the same group that attacked SolarWinds).
Stage 3: Transfer to China (Early 2026)
APT29 sold Coruna to a Chinese hacking group called "Volt Typhoon." The price? Estimated at $15 million in Bitcoin. Volt Typhoon is a professional group linked to the Chinese government.
Stage 4: Widespread Use (March 2026)
Volt Typhoon began using Coruna for widespread attacks. Main targets: government officials, corporate executives, journalists, and human rights activists.
"This is a complete security failure. A tool built to protect us is now being used against us." — Google Threat Intelligence Report
The Victims: 42,000 Infected Devices
As of March 7, 2026, iVerify — a security company offering iPhone scanning tools — confirmed that 42,000 devices have been infected with Coruna. But this is only the number of scanned devices. The actual number is likely much higher.
The geographic distribution of victims shows the attacks were targeted:
| Region | Victim Count | Percentage | Primary Target |
|---|---|---|---|
| United States | 18,500 | 44% | Government officials, executives |
| Europe | 12,000 | 29% | Politicians, journalists |
| Middle East | 7,200 | 17% | Activists, dissidents |
| Asia | 3,100 | 7% | Business competitors |
| Other | 1,200 | 3% | Miscellaneous |
Victims include prominent individuals: US senators, Fortune 500 executives, investigative journalists, and human rights activists. In one case, a US senator's iPhone who was a member of the intelligence committee was infected — and hackers had access to all his communications for 6 months.
Apple's Response: Late But Serious
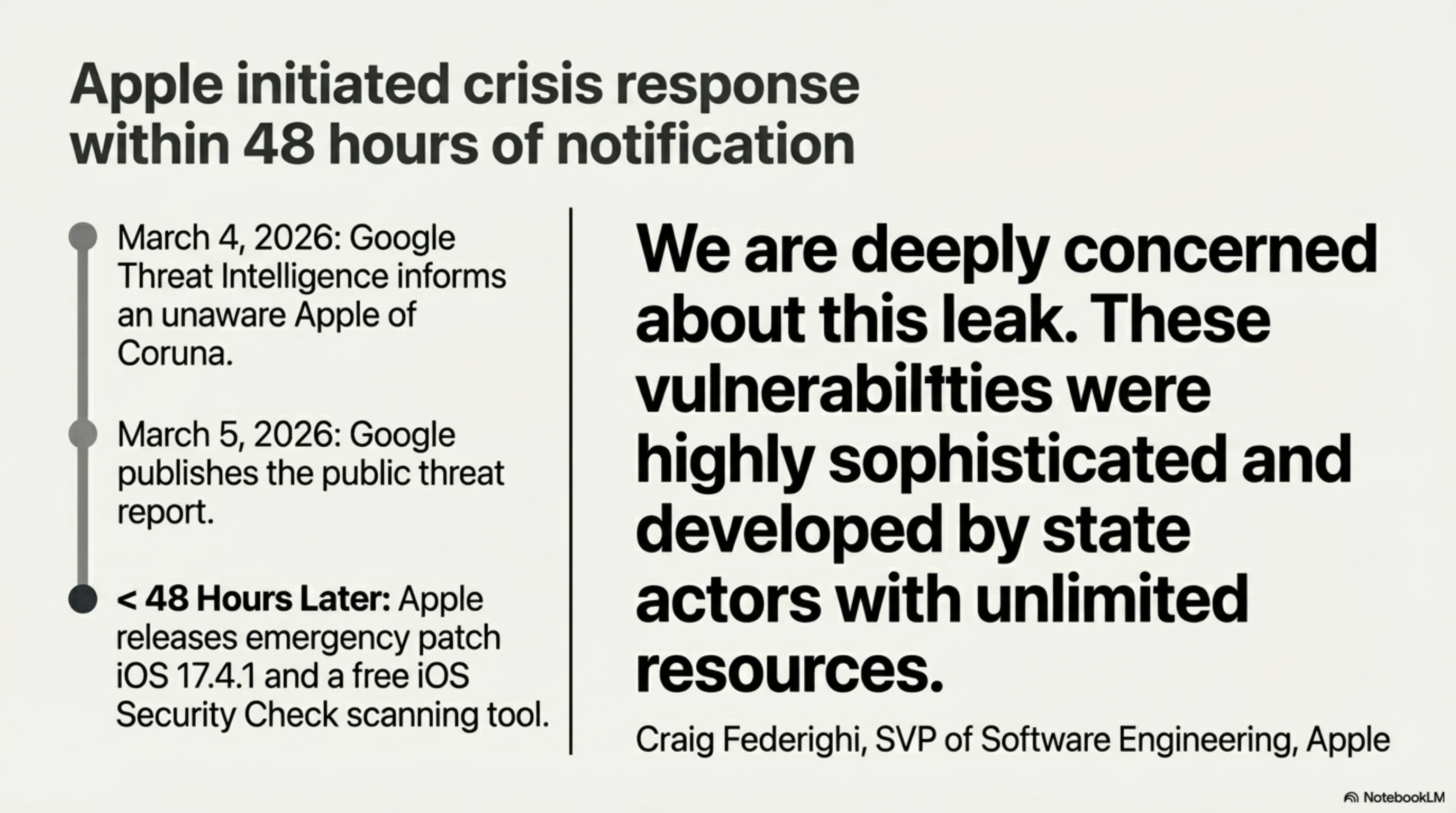
Apple was unaware of Coruna's existence until March 4, 2026. When Google Threat Intelligence informed them, Apple's security team went into crisis mode. Within 48 hours, Apple released an emergency update: iOS 17.4.1.
This update patched all 23 Coruna vulnerabilities. Apple also released a free scanning tool allowing users to check if their device is infected.
But Apple's response faced heavy criticism. Critics ask: Why didn't Apple discover these vulnerabilities earlier? Why did Google have to tell them? Is iOS security really as strong as Apple claims?
Craig Federighi, Apple's Senior Vice President of Software Engineering, said in a statement: "We are deeply concerned about this leak. These vulnerabilities were highly sophisticated and developed by state actors with unlimited resources. We are committed to bringing iOS security to the highest level."
But this response wasn't enough for many. One security analyst wrote: "Apple has claimed for years that iPhone is the world's most secure phone. But Coruna showed this claim was exaggerated."

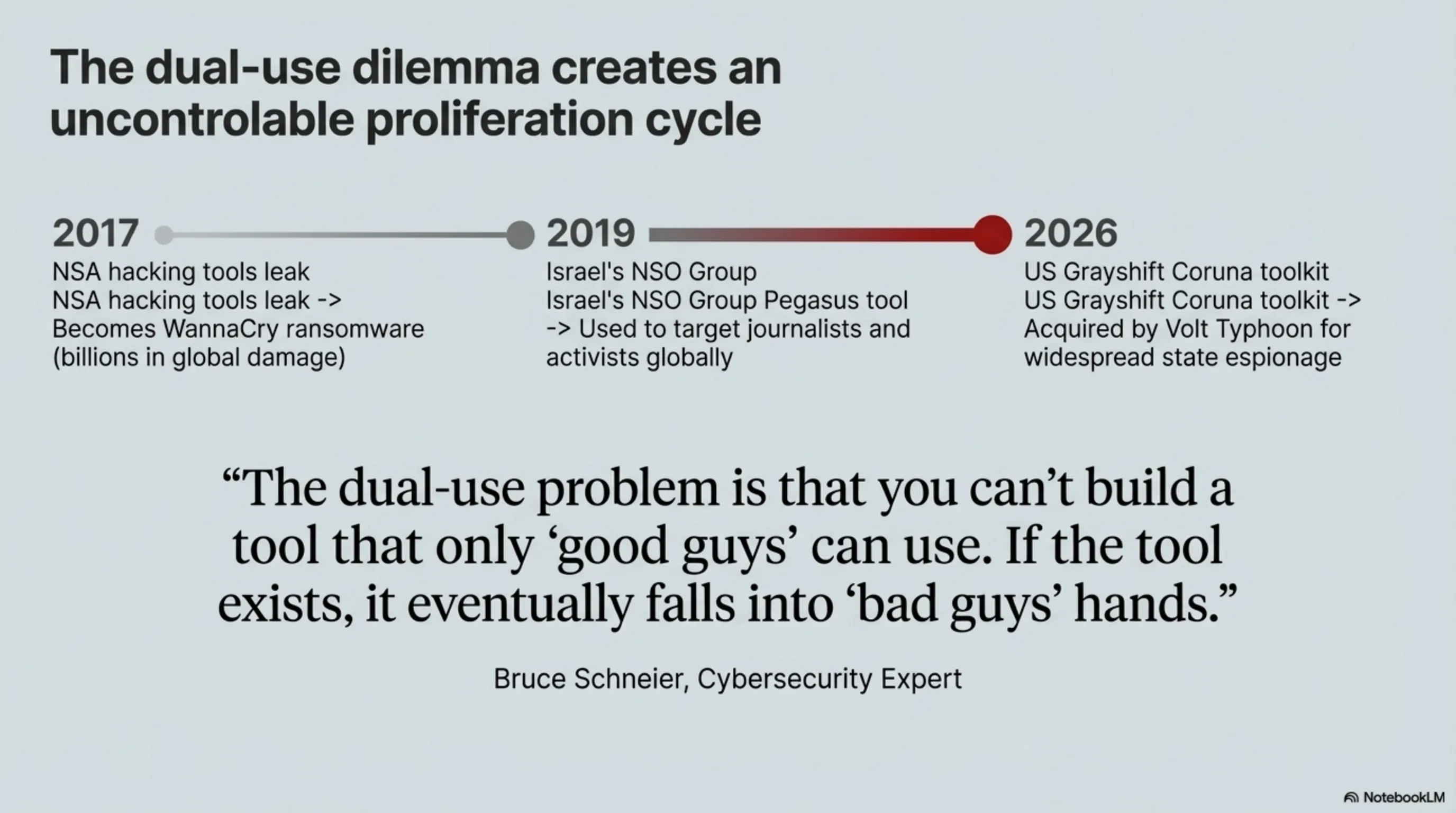
The Dual-Use Problem: When Security Tools Become Weapons
Coruna is a classic example of the "dual-use technology" problem — technologies that can be used for both good and bad purposes. Hacking tools built for intelligence agencies, if leaked, become cyber weapons.
This isn't the first time this has happened. In 2017, NSA hacking tools leaked and became the WannaCry ransomware that caused billions in damage. In 2019, the Pegasus tool from Israel's NSO Group was used to spy on journalists and activists.
Now Coruna has been added to this list. And the big question is: Should governments even build such tools?
Supporters say: Yes, because they're essential for fighting terrorism and espionage. Critics say: No, because the risk of leaking them outweighs their benefits. As we saw in our article on the Great ChatGPT Exodus, when powerful technology falls into the wrong hands, the consequences are catastrophic.
"The dual-use problem is that you can't build a tool that only 'good guys' can use. If the tool exists, it eventually falls into 'bad guys' hands." — Bruce Schneier, Cybersecurity Expert
Government Response: Investigations and Accusations
The US government responded quickly. The FBI launched extensive investigations to find the leak source. The Department of Justice also announced it would file formal charges against Volt Typhoon (the Chinese hacking group).
But China denied these accusations. A Chinese Foreign Ministry spokesperson said: "These accusations are baseless and political. Instead of blaming others, America should strengthen its own security."
Russia also denied any involvement in the Coruna leak. But Google Threat Intelligence evidence shows that APT29 (Russian espionage group) played a key role in transferring Coruna to China.
The US Congress held emergency hearings. Senators asked private security company executives to explain how such a catastrophic leak happened. One senator said: "We give these companies millions of dollars to keep us safe, not to let their tools fall into our enemies' hands."
How to Protect Yourself?
The good news is that Apple has patched Coruna's vulnerabilities. But the bad news is that thousands of infected devices still exist whose users are unaware. Here are some critical steps to protect yourself:
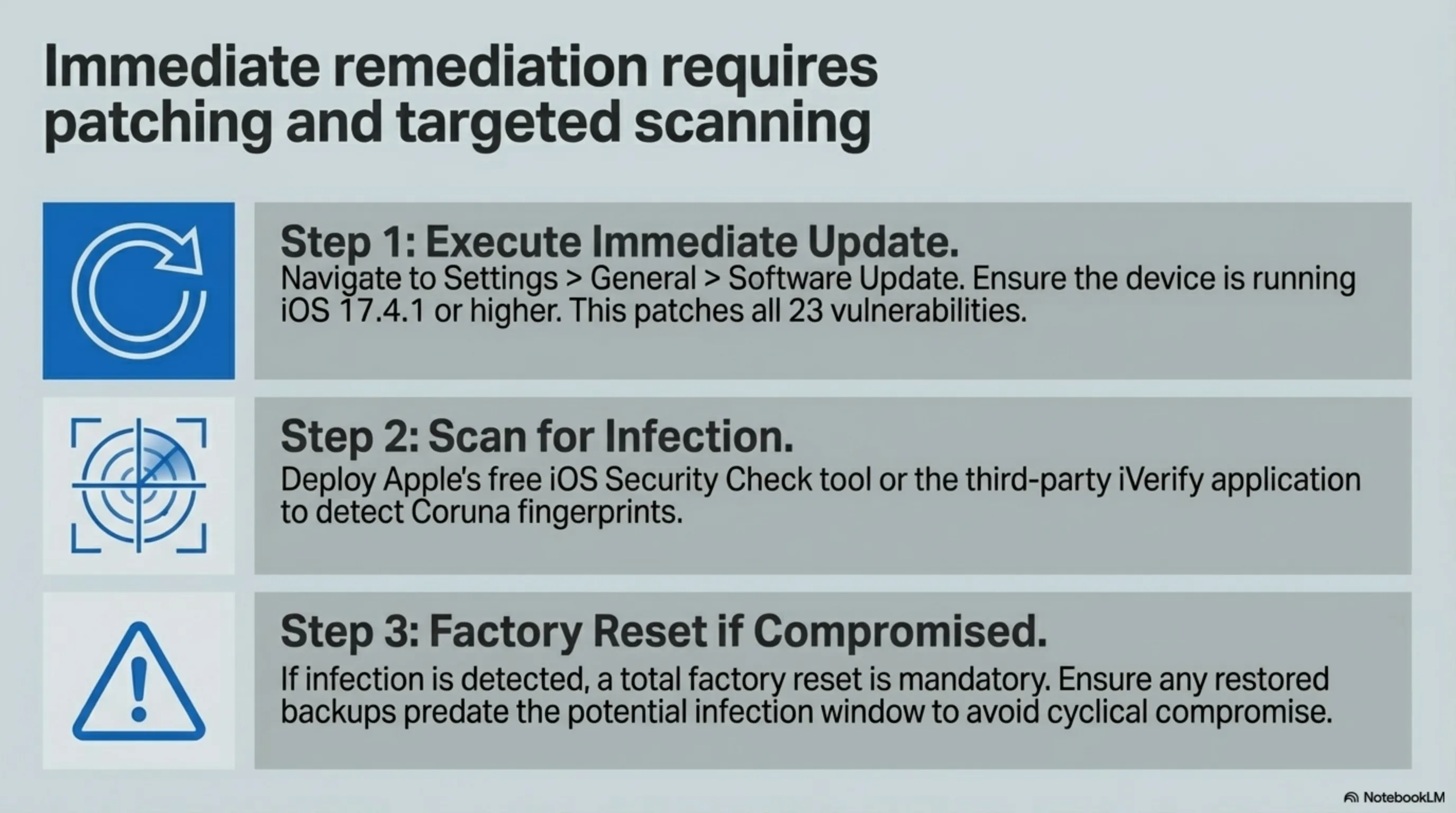
1. Update Immediately: If you don't have iOS 17.4.1 or higher, update right now. This is the most important step. Go to Settings > General > Software Update and install the update.
2. Scan Your Device: Apple released a free tool called "iOS Security Check" that can detect if your device is infected. iVerify also offers a free app that can identify Coruna.
3. If Infected, Do a Complete Reset: If your device is infected, the only solution is a factory reset. Before that, make sure to backup — but ensure your backup isn't infected.
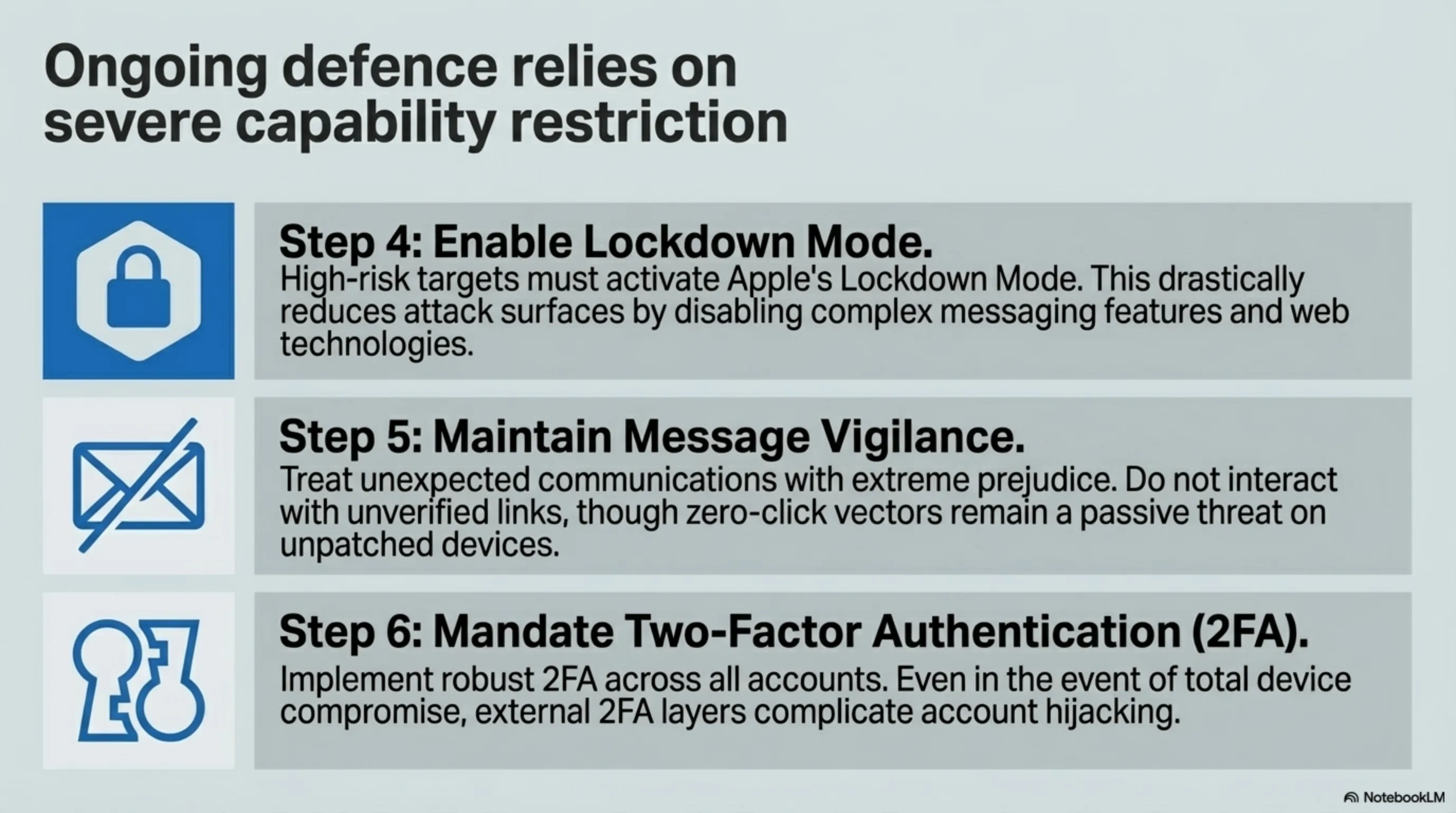
4. Enable Lockdown Mode: Apple has a feature called Lockdown Mode that provides additional protections for high-risk users. This feature limits some capabilities but greatly increases security.
5. Watch for Suspicious Messages: Even with updates, always watch for suspicious messages and links. Never click on links you don't recognize.
6. Enable Two-Factor Authentication: Even if your device is infected, 2FA can prevent hackers from accessing your accounts.
Future Implications: What to Expect?
Coruna likely won't be the last government hacking tool leak. As long as governments build such tools, the risk of leaking exists. And every leak puts millions at risk.
Some experts have called for a complete ban on government hacking tools. They argue that the risk of these tools outweighs their benefits. Others say this is unrealistic — governments will always need such tools.
What's the middle ground? Perhaps more oversight, more transparency, and more accountability. Companies that build hacking tools must have stricter security standards. And governments must be responsible for keeping these tools secure.
Also, tech companies like Apple must invest more in security. Bug bounty programs should be expanded. And cooperation between companies to identify and patch vulnerabilities should increase.
"The future of cybersecurity depends on cooperation. Governments, companies, and users must work together to protect themselves." — Tekin Security Report
Industry Impact: Is iPhone No Longer Secure?
Coruna was a heavy blow to Apple's security reputation. For years, Apple has claimed that iPhone is the world's most secure smartphone. But this leak showed that even iOS is vulnerable.
Apple's competitors quickly seized this opportunity. Google said in a statement: "Android with Google Play Protect and advanced sandboxing offers better security." Samsung also released ads emphasizing Knox security.
But analysts say this is an industry problem, not just an Apple problem. Any operating system can have vulnerabilities. The real problem is that government hacking tools leak and fall into criminals' hands.
One security analyst said: "Coruna showed that no device is 100% secure. But this doesn't mean we should abandon iPhone. It means we should be more realistic and take security more seriously."
Conclusion
Key Takeaway
The Coruna catastrophe showed that when government hacking tools leak, we're all at risk. 23 zero-day vulnerabilities, 42,000 infected devices, and a leak chain from the US government to Russian spies to Chinese hackers — this is the story of a complete security failure.
Apple responded quickly and patched the vulnerabilities. But big questions remain: Why did these vulnerabilities exist in the first place? Why didn't Apple discover them? And most importantly, how can we prevent future leaks?
The main lesson is: No device is 100% secure. But with regular updates, vigilance, and security tools, we can minimize risk. Coruna was a warning — now it's time to take cybersecurity more seriously than ever.
Supplementary Image Gallery: Coruna Catastrophe: US Government iPhone Exploit Kit Leaked to Russian Spies and Chinese Hackers