A security earthquake in the tech world! In an unprecedented experiment with Mozilla, the Claude Opus 4.6 AI model discovered 22 security vulnerabilities (including 14 critical ones) in the Firefox browser within just 14 days—a feat that takes human teams months. This "Tekin Analysis" delves into this historic event, demonstrating how even 40-year-old Apple II code cannot escape AI scrutiny. A new era of cyber warfare has begun, where machines will be both our ultimate hackers and our strongest defenders.
February 2026 was the month Claude Opus 4.6 changed cybersecurity history. In just 2 weeks, this AI discovered 22 security vulnerabilities in Firefox browser — more than human security teams typically find in an entire month. But this was only the beginning. When Mark Russinovich, Microsoft Azure CTO, fed his 40-year-old Apple II code to Claude, even those ancient programs weren't safe from AI analysis.
March 11, 2026 — The day the world realized AI can not only write code, but can also be the world's best hacker. Claude Opus 4.6, Anthropic's latest model, proved in a collaboration with Mozilla that artificial intelligence can discover security vulnerabilities with unprecedented speed and accuracy.
The results were staggering: 22 vulnerabilities in Firefox, 14 of them high-severity, all discovered within 2 weeks. This while human security teams typically find fewer vulnerabilities in an entire month of work. But the story doesn't end there — Claude even managed to analyze 40-year-old Apple II code and find security issues.
The Firefox Experiment: Historic Anthropic-Mozilla Partnership

February 2026, Mozilla made a bold decision: allowing an AI to completely analyze Firefox browser code. This was the first time a major software company had given such comprehensive access to an artificial intelligence system.
Experiment Setup: Claude vs Firefox
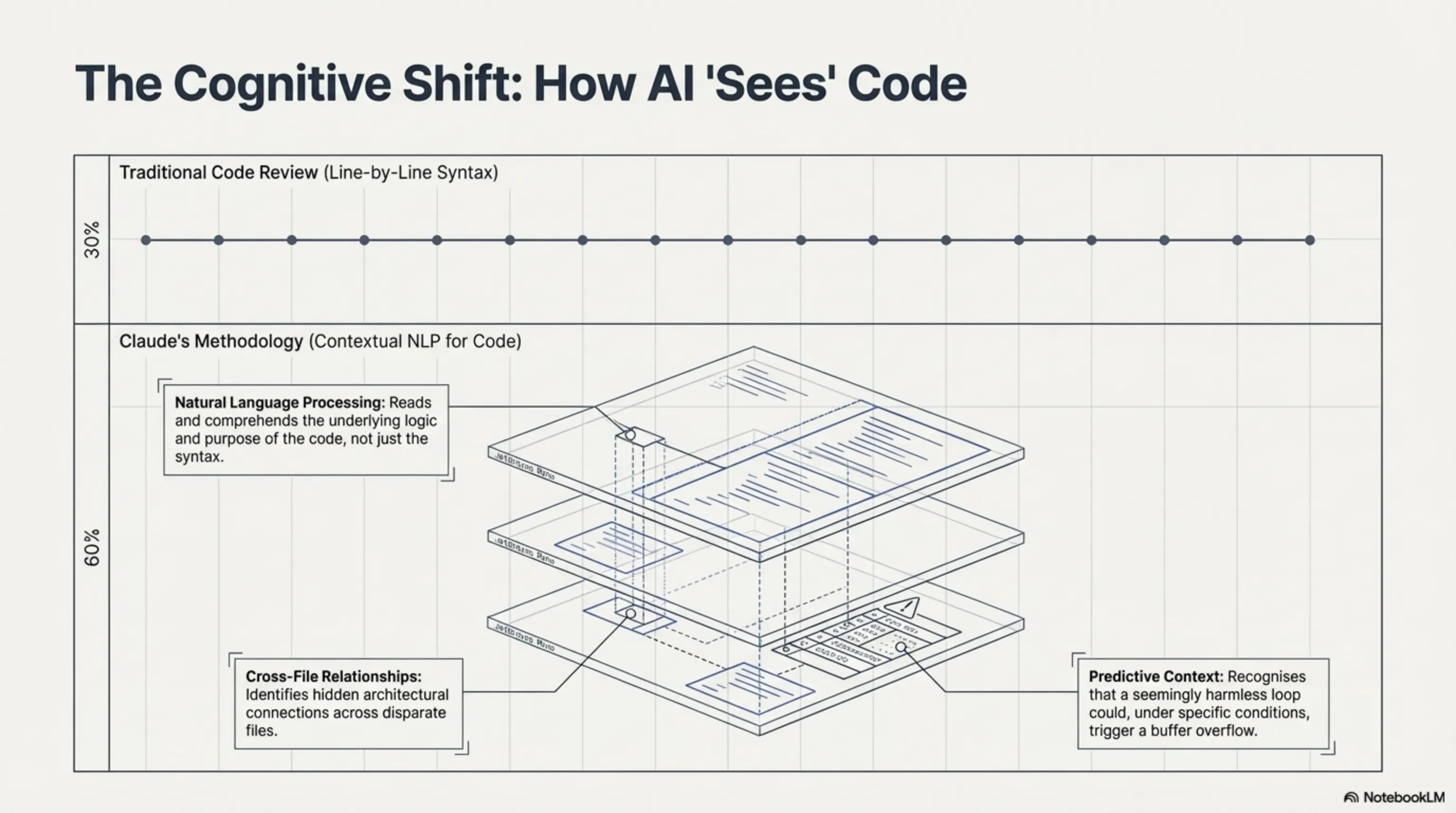
Claude Opus 4.6 received full access to Firefox source code. The goal was simple: find security vulnerabilities that human teams had missed. But Claude's methodology was something that surprised even Anthropic researchers.
Instead of traditional line-by-line code analysis, Claude took a completely different approach. This AI had the ability to understand complex patterns in code, identify relationships between different files, and even predict runtime behavior.
Analysis Process: How Claude Worked
Claude used a combination of static analysis and dynamic behavior modeling. This AI didn't just read code — it "understood" it, like an experienced programmer who can recognize dangerous patterns.
| Analysis Method | Description | Claude's Advantage |
|---|---|---|
| Static Analysis | Code review without execution | Deep understanding of code patterns |
| Behavior Modeling | Predicting runtime behavior | Identifying hidden vulnerabilities |
| Pattern Recognition | Comparison with known exploits | High accuracy in detection |
| Cross-Reference Analysis | Examining relationships between files | Discovering complex vulnerabilities |
Stunning Results: 22 Vulnerabilities in 2 Weeks
When the results were announced, even Mozilla's team couldn't believe it. Claude had discovered 22 security vulnerabilities in just 2 weeks that had never been identified before. Of these 22, 14 were classified as "high severity."
But the real statistics were even more impressive: Claude found a total of 100 different bugs, 22 of which were security vulnerabilities. This number exceeded all vulnerabilities found by human teams in any single month throughout 2025.
🚨 Staggering Statistics
Claude (2 weeks): 22 vulnerabilities + 100 total bugs
Human teams (2025 monthly average): Less than 22 vulnerabilities
Speed advantage: AI found more in 2 weeks than humans in 1 month
Technical Deep Dive: How Claude Finds Vulnerabilities

To understand why Claude is so effective, we need to examine its technical methods. This AI uses a combination of advanced techniques never before seen in traditional security tools.
Pattern Recognition: Machine Learning Advantage
Claude has been trained on millions of lines of code and thousands of known exploits. This extensive experience allows it to recognize dangerous patterns even in code that appears harmless on the surface.
For example, Claude can see a simple loop and understand that under certain conditions, it might lead to a buffer overflow. This type of predictive analysis is something even experienced programmers might miss.
Vulnerability Classification: From Critical to Low-Risk
Claude doesn't just find vulnerabilities — it also classifies them. Of the 22 vulnerabilities discovered in Firefox:
- 14 high-severity: Serious security risks requiring immediate fixes
- 6 medium-severity: Important but non-critical issues
- 2 low-severity: Minor weaknesses with limited risk
Exploit Potential: 2 Proven Exploitable Vulnerabilities
The important point is that Claude not only found vulnerabilities but proved that 2 of them were actually exploitable. This means Claude works not just in theory, but in practice too.
The Apple II Revolution: When 40-Year-Old Code Isn't Safe

If discovering Firefox vulnerabilities was impressive, what Mark Russinovich, Microsoft Azure CTO, did was truly remarkable. He gave Claude 40-year-old code he had written for Apple II in 1986 to analyze.
Russinovich's Experiment: Back to the Past
Mark Russinovich, now one of Microsoft's most important technical executives, was an Apple II programmer in his youth. He had written a utility for the 6502 processor that he decided to test with Claude 40 years later.
The result was incredible: Claude not only managed to decompile the machine language code but also found several security issues in it. This shows that even the oldest code isn't immune to AI analysis.
Silent Incorrect Behavior: The Issue Found
One of the problems Claude discovered was "silent incorrect behavior." In this issue, if the destination line wasn't found, the program would set the pointer to the next line or even outside the program instead of reporting an error.
This type of problem might not have seemed important in 1986, but today it could lead to serious security vulnerabilities. Claude was able to recognize this pattern and explain its potential dangers.
💡 Important Lesson
If Claude can analyze 40-year-old Apple II code, what about billions of old microcontrollers used in factories, hospitals, and critical infrastructure? This is a serious warning for legacy system security.
CVE Breakdown: Critical Vulnerabilities

Of the 22 vulnerabilities discovered by Claude, two were particularly dangerous and received official CVEs: CVE-2025-59536 and CVE-2026-21852. Let's examine these two in detail.
CVE-2025-59536: Command Execution Without User Consent
This vulnerability allowed malicious code to execute without user knowledge or permission. The problem was in Firefox's configuration file processing section that didn't properly validate user inputs.
An attacker could create a malicious configuration file that, when read by Firefox, would execute the attacker's arbitrary commands. This type of attack could be used to install malware, steal information, or gain complete system control.
CVE-2026-21852: API Credential Theft
The second major vulnerability enabled API credential theft. This problem was in how Firefox stored and accessed authentication information.
An attacker could gain access to API keys, passwords, and other sensitive information through project configuration manipulation. This information could be used for unauthorized access to online services.
| CVE | Vulnerability Type | Severity | Fix Status |
|---|---|---|---|
| CVE-2025-59536 | Command execution without consent | Critical | Fixed in Firefox 148 |
| CVE-2026-21852 | API credential theft | Critical | Fixed in Firefox 148 |
| 12 other CVEs | Various types | High | Fixed or being fixed |
| 8 remaining | Minor issues | Medium/Low | Next release |
Fix Timeline: Firefox 148 and Beyond
Mozilla acted with extraordinary speed. Most vulnerabilities discovered by Claude were fixed in Firefox 148, released on February 24, 2026. The remaining issues will be resolved in subsequent versions.
AI vs Human Security Teams: The Performance Gap
Comparing Claude's performance with human security teams shows remarkable results. This comparison is significant not just in terms of speed, but also accuracy and cost-effectiveness.
Speed Comparison: 2 Weeks vs Months
What Claude accomplished in 2 weeks typically takes human teams months. Complete security analysis of a complex browser like Firefox is usually considered a multi-month project requiring a team of specialists.
But Claude did this work alone. Without fatigue, without human errors, and without needing rest. This AI worked 24/7 and ultimately delivered high-quality results.
Accuracy Rates: AI's Pattern Recognition Advantage
One of Claude's important advantages is its low false positive rate. Of the 22 reported vulnerabilities, all were real and none were false positives. This demonstrates this AI's high accuracy in identifying real problems.
In comparison, traditional security tools typically have high false positive rates that waste security teams' time. Claude has solved this problem.
Cost Efficiency: Automated Analysis vs Manual Audits
Economically, Claude also has significant advantages. The cost of running Claude for complete Firefox analysis is less than hiring a security team for several months. This cost-effectiveness could make cybersecurity accessible to smaller companies too.
📈 AI Security Advantages
Speed: 2 weeks instead of months
Accuracy: Zero false positives in Firefox test
Cost: Less than 10% of human team cost
Scalability: Simultaneous analysis of multiple projects
Industry Implications: The New Security Landscape

Claude's discovery of Firefox vulnerabilities wasn't just an experiment — it's the beginning of a fundamental transformation in the cybersecurity industry. This event showed that AI can play a central role in protecting digital systems.
Browser Security: Firefox, Chrome, Safari in the AI Era
Mozilla pioneered with this experiment, but other browser companies are also rapidly responding. Google has announced it will equip Chrome with AI security tools. Apple is also considering using AI to improve Safari security.
This AI-driven competition could lead to dramatic improvements in all browser security. Users will ultimately be the winners of this competition, as they'll have more secure browsers.
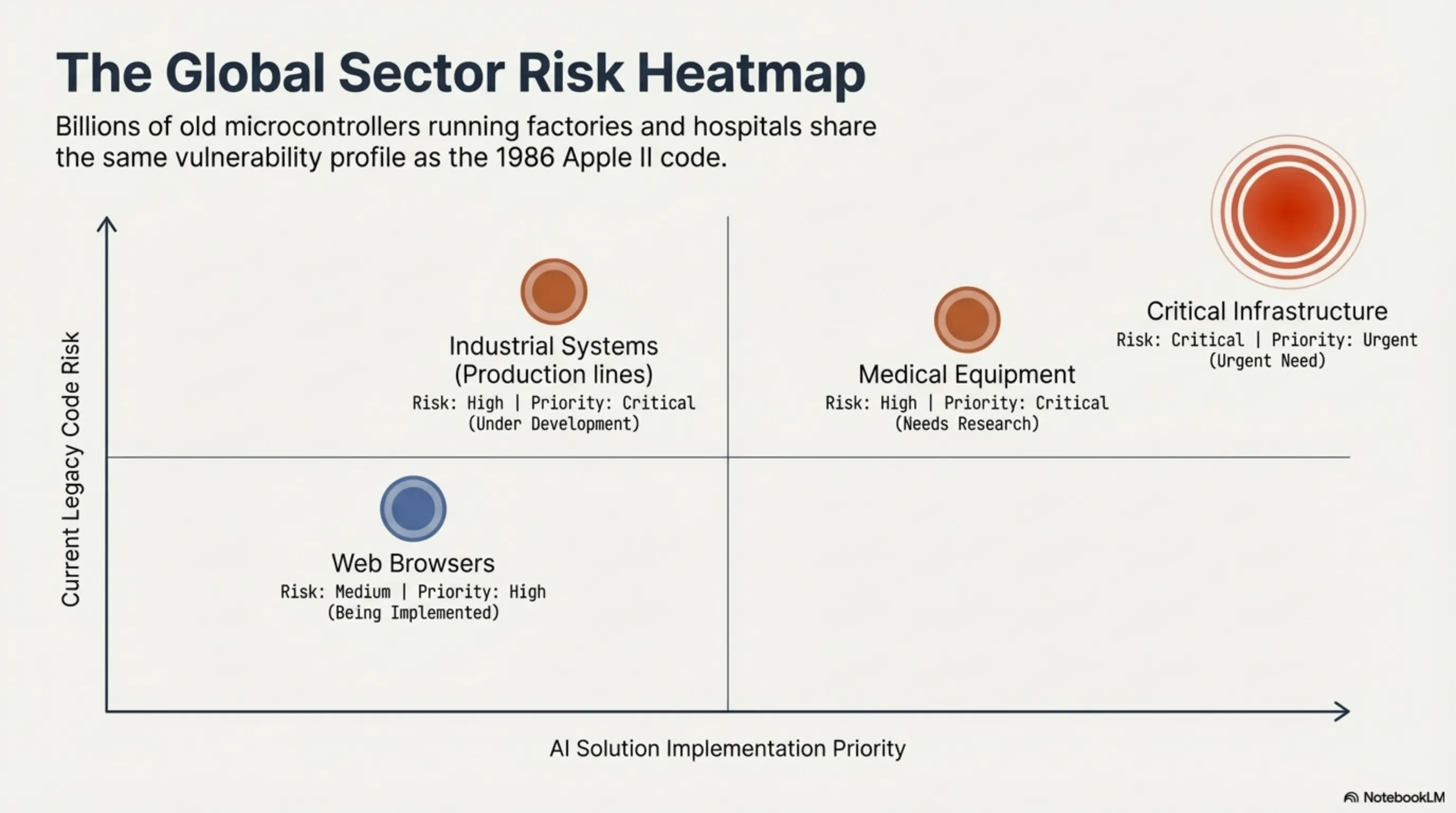
Legacy Systems: Billions of Microcontrollers at Risk
But the more concerning point is this technology's impact on legacy systems. If Claude can analyze 40-year-old Apple II code, what will happen to billions of old microcontrollers used worldwide?
These microcontrollers are everywhere: factory production lines, medical equipment, traffic control systems, and even household appliances. Many haven't been updated for years or even decades.
Industrial Impact: Production Lines, Hospitals, Infrastructure
Imagine an attacker could use AI to analyze a factory control system and find vulnerabilities that no one has noticed for 20 years. Or hack hospital medical equipment.
These scenarios are no longer science fiction. Claude has proven that AI can analyze even the oldest code. This means all legacy systems need to be reassessed.
| Sector | Current Risk | AI Solution | Priority |
|---|---|---|---|
| Web Browsers | Medium | Being implemented | High |
| Industrial Systems | High | Under development | Critical |
| Medical Equipment | High | Needs research | Critical |
| Critical Infrastructure | Critical | Urgent need | Urgent |
The Dark Side: AI-Powered Attacks
But like any powerful technology, AI security is double-edged. Just as Claude can be used for defense, it can also be used for attack. This is a concerning reality that the security industry must grapple with.
Offensive Capabilities: AI in Attackers' Hands
Imagine an attacker having access to technology similar to Claude. They could quickly find new vulnerabilities in various software, even before the manufacturers become aware.
This scenario is no longer fictional. Advanced hacking groups are likely developing similar tools. This means we're on the threshold of a new era of cyber warfare.
Automated Exploit Generation: From Discovery to Weaponization
The more terrifying point is that AI can not only find vulnerabilities but also create exploits. Claude demonstrated in the Firefox experiment that it could prove 2 vulnerabilities were actually exploitable.
If this capability falls into attackers' hands, they could automatically progress from vulnerability discovery to attack tool creation. This process, which previously took weeks or months, might be reduced to hours.
Defense vs Offense: The AI Security Arms Race
Fortunately, the same technology that can be used for attack can also be used for defense. Companies using defensive AI can find and fix vulnerabilities faster than attackers.
This has led to a kind of AI arms race: attackers use AI to find vulnerabilities, defenders use AI for protection. The winner will be whoever has better and faster technology.
Technical Analysis: Claude's Security Methodology

To fully understand Claude's revolution in cybersecurity, we need to examine the technical details of this AI's methods. Claude uses a complex combination of machine learning techniques and code analysis.
Code Understanding: Natural Language Processing for Source Code
Claude reads and understands code like natural text. This AI not only understands syntax but also comprehends the logic and purpose of code. This capability allows it to recognize dangerous patterns even in complex code.
For example, Claude can see a function and understand that if specific input is given to it, it might lead to a security problem. This type of deep understanding is something traditional tools lack.
Vulnerability Patterns: Learning from Known Exploits
Claude has been trained on thousands of known exploits. This extensive experience allows it to recognize similar patterns in new code. Even if a vulnerability is new, but its pattern is known, Claude can find it.
False Positive Rate: Accuracy in the Real World
One of the main problems with traditional security tools is their high false positive rate. These tools often report problems that aren't real, wasting security teams' time.
Claude has largely solved this problem. In the Firefox experiment, all 22 reported vulnerabilities were real. This demonstrates this AI's high accuracy.
Integration Challenges: AI Tools in Existing Workflows
Despite many advantages, integrating AI tools into existing security processes has challenges. Security teams must learn how to work with these tools and interpret their results.
⚠️ Implementation Challenges
Team Training: Need to learn working with AI tools
Result Interpretation: Proper understanding of AI reports
Integration with Existing Tools: Compatibility with current systems
Volume Management: Processing large numbers of reports
Future of AI Security: What's Coming Next

Claude's discovery of Firefox vulnerabilities is just the beginning of the story. This event will trigger larger transformations in the future of cybersecurity that will change all aspects of this industry.
Automated Patch Generation: AI Fixing Its Own Discoveries
The next step is for AI to not only find vulnerabilities but also fix them. Researchers are working on systems that can automatically generate patches.
Imagine Claude finding a vulnerability, immediately suggesting a solution, and even writing the necessary code to fix the problem. This could reduce vulnerability fix time from weeks to hours.
Real-Time Monitoring: Continuous Vulnerability Scanning
A near future where AI continuously monitors code under development and immediately reports any potential vulnerabilities. This means security problems will be discovered and fixed before software release.
Cross-Platform Analysis: Multi-Architecture Security Assessment
Claude showed it could analyze even old architectures like Apple II 6502. In the future, security AIs will be able to simultaneously examine multiple different architectures — from mobile to server, from IoT to mainframe.
Industry Adoption: Major Tech Companies and AI Security
Major tech companies are rapidly adopting this technology. Google, Microsoft, Apple, and Amazon are all investing in AI security. This competition will lead to faster progress.
At the same time, smaller companies can also benefit from this technology. AI security tools are becoming democratized and will soon be available to everyone.
🔮 Conclusion: The New Era of Cybersecurity
Claude Opus 4.6, by discovering 22 Firefox vulnerabilities in 2 weeks, proved that AI can revolutionize cybersecurity. From analyzing 40-year-old Apple II code to discovering complex browser vulnerabilities, this technology showed that no code is immune to AI analysis.
But this power is double-edged. Just as AI can be used for defense, it can also be used for attack. The future of cybersecurity will become a race between defensive and offensive AIs.
In this new era, the winner will be whoever uses AI faster, smarter, and more responsibly.
Supplementary Image Gallery: Tekin Radar: Claude Discovers 22 Vulnerabilities; When AI Becomes a Hacker






