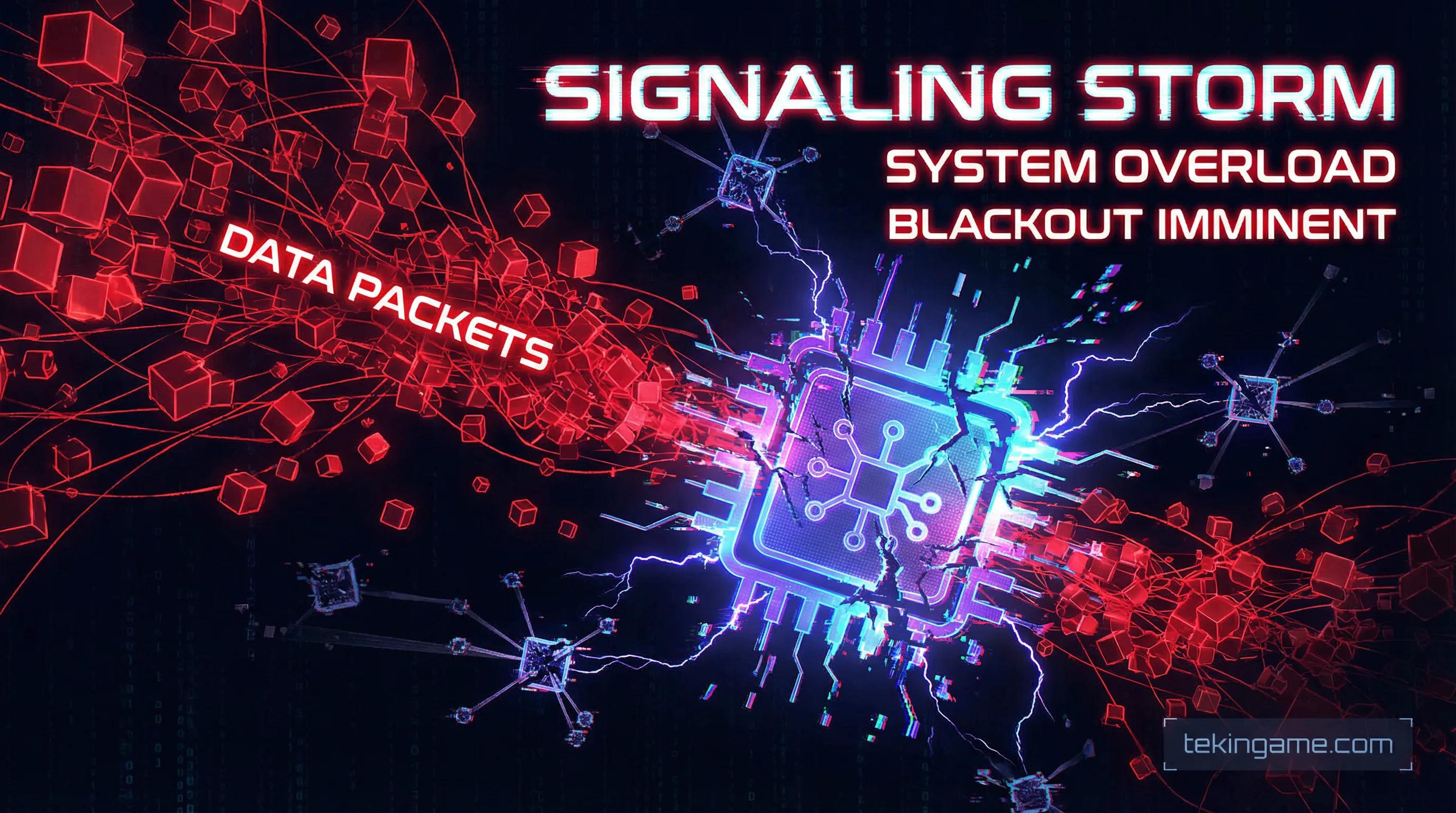
Crisis Level: On February 20, 2026, Singapore officially confirmed that the Core Networks of its four major mobile operators were compromised by Beijing-affiliated Advanced Persistent Threat (APT) groups. - Attack Vector: The threat actors bypassed AI-driven Intrusion Detection Systems (IDS) in 5G networks by exploiting SS7/Diameter protocol vulnerabilities, executing BGP Hijacking, and utilizing LotL (Living off the Land) techniques. - Strategic Objective: This was not a financial ransomware operation. It was a "tactical m
1. Introduction: The Day Asia's Digital Fortress Fell
In the technology realm, Singapore is the equivalent of "Fort Knox." It is a digital fortress where the financial traffic, cloud servers, and sensitive data of half the world's tech giants flow through its fiber optics and submarine cables. However, the security bulletin issued on February 20, 2026, shattered the illusion of "absolute security." The official confirmation of a simultaneous breach into the core networks of the country's four major telecommunications operators by Chinese state-sponsored hackers is more than just a cyber incident; it is the starting gun for the offensive phase of the modern Digital Cold War.
At Tekin Analysis, we do not settle for surface-level headlines. Hacking a mobile operator is fundamentally different from breaching a website or even a bank. When attackers reach the Core Network, they do not merely steal data; they gain the power to reroute a nation's traffic, intercept encrypted communications in real-time, and paralyze critical energy and transportation infrastructures. In this special dossier, we put the digital magnifying glass on exactly how the Red Dragon slipped past 5G firewalls and why this event should keep telecom executives in the Middle East and Europe awake at night.
\n2. Anatomy of the Breach: Warfare in the Shadows and Evading AI
Let’s step away from Hollywood hacker illusions. Beijing's state-sponsored hackers (highly evolved factions of APT41 and Volt Typhoon) do not attack with black screens and raining green code. They live inside the victim's systems for months with lethal patience. Forensic investigations in Singapore’s security labs reveal that the Dwell Time (the period the hackers remained undetected in the network) for this combined attack was over 280 days! But how did four major operators, equipped with the most expensive Next-Generation Firewalls (NGFW) and Endpoint Detection and Response (EDR) systems, miss this?
The Kill Chain: From the Edge to the 5G Core
To bypass security layers, the attackers employed a terrifying strategy known as Living off the Land (LotL). In this attack architecture, the hacker introduces no new malware, trojans, or ransomware that might trigger antivirus alarms. They do not break down security walls; instead, they steal the "master key" and walk the corridors wearing the guards' uniforms.
- Phase 1 - Initial Access: The attack began by exploiting unpatched Zero-Day and N-Day vulnerabilities in edge network devices, specifically enterprise VPN gateways (such as legacy Fortinet or Pulse Secure appliances). These unpatched gateways became open tunnels into the DMZ.
- Phase 2 - Fileless Execution: Rather than writing malware to the servers' hard drives, the hackers executed their code directly in the volatile memory (RAM). Every server reboot wiped their tracks, but they persistently returned to memory via hidden backdoors.
- Phase 3 - Lateral Movement: They utilized legitimate administrative tools already present on Singaporean systems—such as PowerShell, WMI (Windows Management Instrumentation), and network monitoring protocols—to move through the network. AI-driven Network Detection and Response (NDR) algorithms simply whitelisted these activities as "routine administrative traffic."
- Phase 4 - Breaching the Core: Their ultimate target wasn't the customer CRM database. They bypassed peripheral networks and moved straight for the brain: the 5G Core (5GC) and the HLR/HSS servers (which store all SIM identity data). At that moment, strategic control of Singapore's communication arteries fell into Beijing's hands.

3. The Ancient Protocol Catastrophe: Weaponizing SS7 and BGP
The biggest commercial lie sold by telecom vendors (like Ericsson, Nokia, Cisco, and Huawei) to governments is this: "5G networks are impenetrable due to their Cloud-Native architecture and End-to-End encryption." Yes, the radio encryption between your smartphone and the cell tower (RAN) is highly secure. But the catastrophe occurs deep within the Core Network. When a 5G network needs to route a roaming SMS, a bank verification code, or an international call, it must time-travel back to the 1980s and use ancient protocols like SS7 (Signaling System No. 7) and its slightly modern but still vulnerable sibling, Diameter.
Network Poisoning via SS7
SS7 was designed in 1975, an era before the public internet, when telecom networks were controlled by a few trusted state monopolies. Thus, the protocol's fatal flaw is its reliance on "absolute trust." Chinese hackers exploited this Achilles' heel perfectly.
By infiltrating international Signaling Hubs in third-party countries with weaker security, they spoofed their identity to appear as a "legitimate foreign operator." With this fake identity, they sent malicious Update Location Requests (ULR) to Singapore's servers. Trusting the protocol, Singapore's network complied. The result? The attackers intercepted SMS Two-Factor Authentication (2FA) codes of high-ranking financial executives, government officials, and Western diplomats in real-time, without installing a single piece of spyware on the victims' phones. Furthermore, via Cell-Tower Triangulation, they tracked the exact street-level movements of strategic targets.

BGP Hijacking: Daylight Robbery of National Traffic
While SS7 was used for targeted espionage, China needed a more devastating tool for mass data interception: BGP (Border Gateway Protocol) Hijacking. BGP is the compass of the global internet, dictating how data travels between countries via submarine cables. By poisoning the global routing tables along critical submarine cable systems (like SeaMeWe-3) passing through Singapore, the PLA hackers executed a massive Man-in-the-Middle (MitM) attack.
Instead of Singaporean government traffic routing directly to servers in California or London, the poisoned routers declared: "The fastest route to the US is through China Telecom's servers in Beijing!" Traffic was siphoned into China in a hidden loop, inspected, copied, and injected back into its original path with negligible latency. It took threat hunters months to detect this geopolitical-scale interception by analyzing anomalous TTL (Time to Live) packet data.
4. The Doomsday Scenario: A Geopolitical Prelude to War
Amateur analysts on social media believe the goal was merely citizen data theft or financial extortion. At Tekin Analysis, we dismiss such naivety. When the People's Liberation Army (PLA) and its cyber units (specifically Unit 61398) focus their astronomical computing resources on Singapore—the economic beating heart of Asia and the world's most critical submarine cable intersection—the objectives are strictly geopolitical.
Our intelligence assessment reveals three macro-level military objectives:
- Cyber Cartography for the Taiwan Crisis: China is running digital simulations for a "Taiwan Doomsday" scenario. In the event of a kinetic conflict over Taiwan, the US Pacific Fleet and NATO rely heavily on the communication and maritime logistics networks of Southeast Asia. Hackers infiltrated Singapore to map the exact topology of its 5G networks. They now know precisely which routers and data centers to blind with heavy cyberattacks to paralyze Western military communications in the region.
- Planting Logic Bombs and Dormant Backdoors: Upon reaching the Core layer, the attackers did not just extract data; they injected dormant malware and Logic Bombs into the firmware of critical equipment. These malicious codes appear harmless during security audits. However, they are programmed to wake up upon receiving a hidden cryptographic pulse from Command and Control (C2) servers in Beijing, instantly wiping the firmware and "bricking" the hardware, causing a physical network collapse that would take weeks to recover.
- Testing the Signaling Storm: This was a cyber military drill. They tested a critical theory: If, at hour zero of a war, they send millions of rapid, fake Attach Requests to the operators' authentication servers (HLR/HSS), can they overload the 5G core in seconds and plunge the entire country into an absolute communications blackout? Tragically for the free world, the answer was yes.

5. The Middle East Blast Wave: The Achilles Heel of Gulf Telcos

Here is where the alarm bells should deafen the Middle East. If Singapore—a nation with multi-billion-dollar cyber defense budgets, a draconian Cyber Security Agency (CSA), and direct intelligence-sharing with the NSA and GCHQ—can be brought to its knees so effortlessly, what is the fate of telecom operators in the MENA (Middle East and North Africa) region?
The Technological Frankenstein Syndrome
The naked truth is that the network architecture in many Gulf states suffers from a "Technological Frankenstein Syndrome." Due to shifting budgets, rapid expansions, and political pressures, the Core and Radio Access Networks (RAN) are often a dangerous hodgepodge of incompatible technologies. Legacy 3G/4G infrastructure runs parallel to 5G, mixing asymmetric western equipment (Ericsson, Nokia) with cheaper eastern hardware (Huawei, ZTE). This lack of architectural cohesion creates catastrophic security gaps in Protocol Translation layers.
When the Middle East's critical energy infrastructure—massive refineries, oil wells, desalination plants, and smart grids in mega-projects like NEOM—relies on local mobile networks (IoT & M2M) to transmit SCADA/ICS telemetry data, a hacked telco is no longer just a dropped smartphone call. It means hackers can physically shut down crude oil transfer pumps in the Persian Gulf! The absence of continuous aggressive Red Teaming and blind reliance on passive firewalls make Middle Eastern operators glowing, moving targets in the digital cold war.
6. Tekin's Final Verdict: The Survival Guide for the Cyber War Era
The fall of Singapore's digital fortress on February 20, 2026, sends a historic and bitter message to all tech leaders: The era of "Castle and Moat" cybersecurity is officially dead. World War III will not begin in the halls of the UN or with the launch of ballistic missiles; it will begin with the poisoning of submarine BGP tables and the blackout of 5G servers.
Chief Information Security Officers (CISOs) in telcos, banks, and strategic organizations must bulldoze their defense strategies and rebuild from scratch. In this ruthless ecosystem where nation-states have entered the offensive hacking phase, the following measures are no longer optional "projects"—they are absolute imperatives for survival:
- Unconditional Migration to Zero-Trust Architecture: No device, not even the central router sitting in the operator's most secure subterranean data center, should be trusted by default. The concept of a "secure internal network" is a myth. Every data packet, system request, and user must undergo Continuous Authentication.
- Deploying AI-NDR (Network Detection & Response): Traditional firewalls are blind to LotL attacks. Networks require AI-driven hunters capable of identifying hidden behavioral patterns and microsecond anomalies in encrypted traffic, severing connections to C2 servers before commands are executed.
- Micro-Segmentation: If a hacker breaches the administrative HR network, shifting to the 5G Core must be technically impossible. Networks must be software-segmented with the strictest Least Privilege access rules.
- Transitioning to Quantum-Safe Cryptography: With the breakneck speed of quantum computing advancements in China and the US, current key exchange protocols (RSA/ECC) will expire within years. Hackers are currently stealing encrypted data to decrypt it later (Harvest Now, Decrypt Later). Forward-thinking operators must invest in Quantum Key Distribution (QKD) networks today.
The year 2026 has officially proven that on the global digital map, there are no neutral countries. In this new cold war, you are either equipped with cyber armor, or you simply cease to exist.
\nFinal Verdict
TekinGame Command Room Verdict
- Infiltration via Blind Spots: Hackers exploited ancient SS7 and BGP protocols to bypass Singapore's advanced 5G AI firewalls.
- Beyond a Simple Hack: This breach was not for financial gain; it was strategic espionage and preparation for future conflicts, particularly concerning Taiwan.
- A Lesson for the Middle East: Regional operators with fragmented infrastructure ("Technological Frankenstein Syndrome") are highly vulnerable targets for this new wave of cyber warfare.
- The Only Way Forward: Immediate implementation of Zero-Trust architecture, AI-driven behavioral monitoring, and quantum-safe cryptography.
What are your thoughts? Do you feel your local operator is equipped to handle this level of cyber threat? Share your opinions in the comments below.
