The gaming world is no longer just entertainment; it is a multi-billion-dollar economy. Today, gamers invest thousands of dollars into their accounts—from CS:GO skins to massive Steam and PSN libraries. This makes them highly lucrative targets for hackers and cybercrime syndicates. In this Tekin Garage mega-article, the Chief Inspector dissects the latest cyber threats (Discord phishing, malware hidden in cheats and cracked games) and provides actionable strategies to make your "Digital Fortress" absolutely impenetrable.
Welcome to the Tekin Garage Strategic War Room. Comrades, let’s debug a cold hard truth: modern hackers aren't trying to crash your Windows anymore; they are hunting for your "Digital Identity." Today, your Steam, PlayStation Network (PSN), or Valorant account is not just a gaming profile; it is a "Hot Wallet" containing hundreds of hours of effort and thousands of dollars in real-world value.
In 2026, hackers use AI-driven tools and next-gen malware to design attacks that can dismantle even the most cautious users. The Chief Inspector of Tekin Garage is here today to rebuild your defense systems from the Kernel layer to the cognitive layer. This is your survival manifesto in the cyber wilderness.
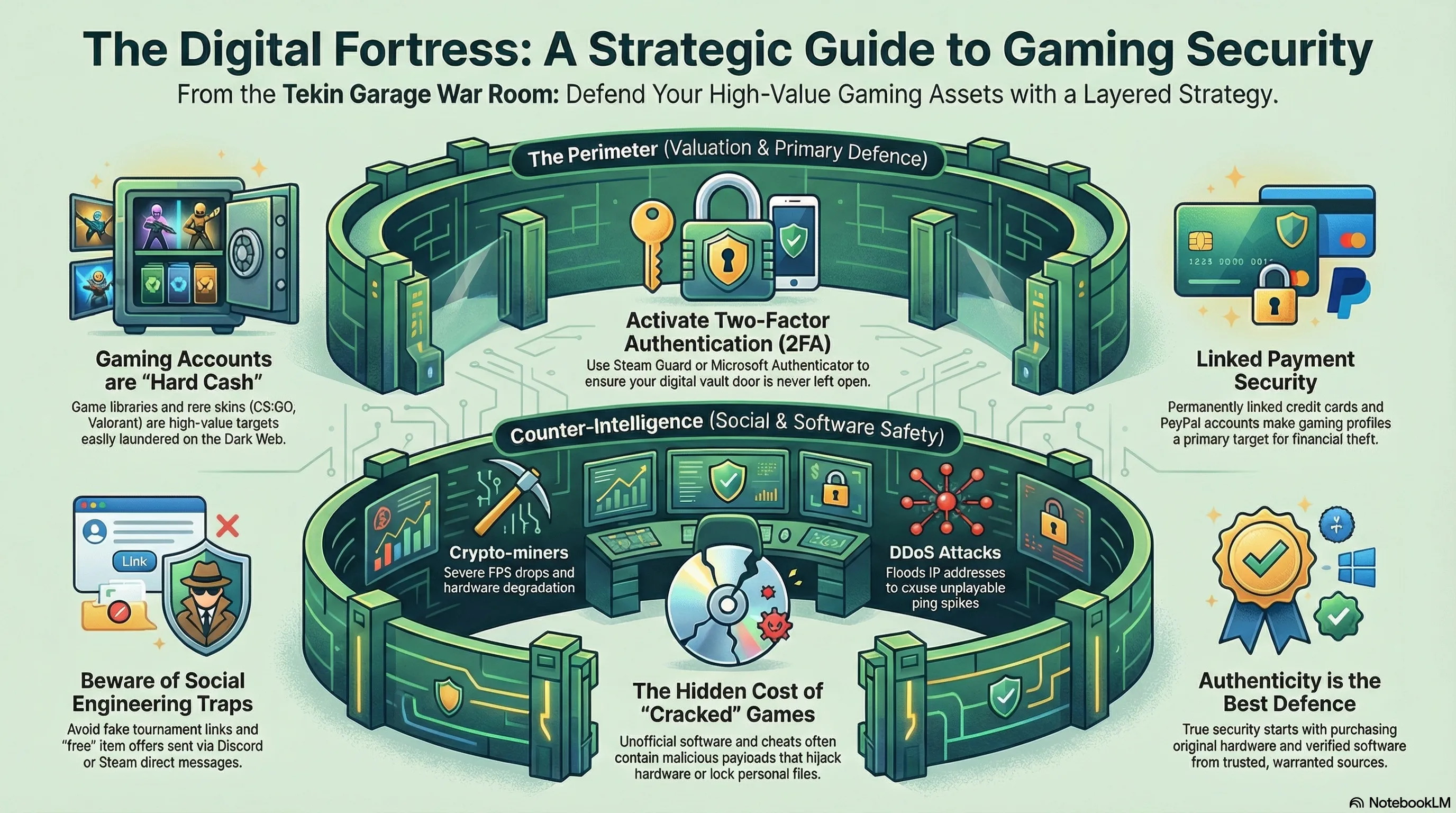
1. Layer One: Dissecting the Shadow Economy; Why You are Target #1
Many gamers suffer from a legacy mindset, thinking that being hacked only happens to the famous or the wealthy. In the underground economy of the Dark Web, gaming accounts are treated as "Liquid Assets" that are easily laundered without banking red tape. Here is why hackers love you:
- Instant Liquidity: Rare skins in games like CS2 or Rust can be instantly converted into cryptocurrency on third-party marketplaces. Hackers don't need your bank account; they steal your skins and cash out in five minutes.
- Hardware Hijacking (Crypto-jacking): Your high-end gaming rig is a juicy prize for stealthy cryptocurrency mining. Hackers would rather mine Bitcoin using your expensive GPU than ask you for a ransom.
- Pivot Attacks: Your gaming account is the "anchor" of your digital life. Once a hacker breaches your Steam or Discord, they use it to pivot into your primary email, mobile number, and linked credit cards.
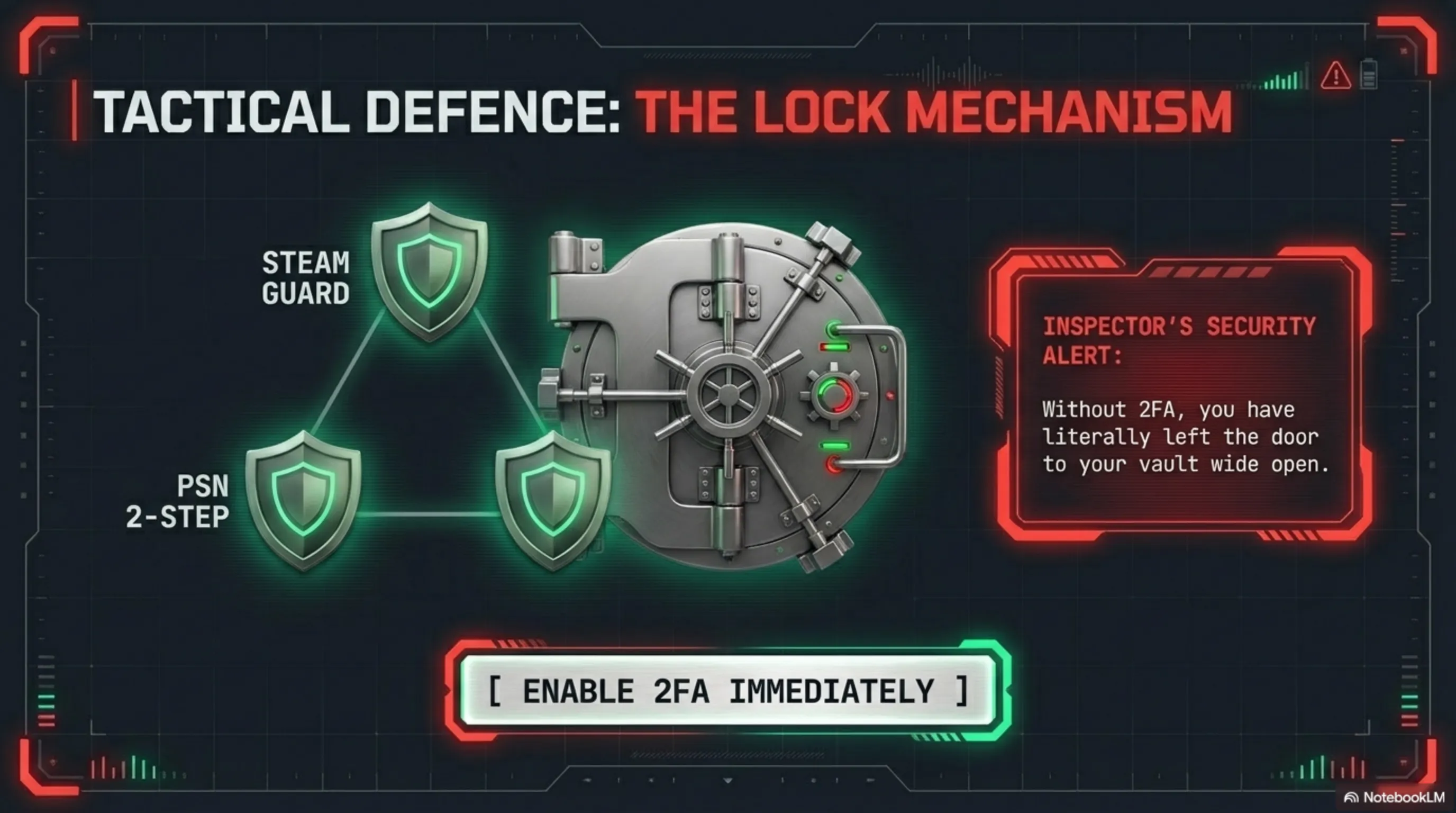
🚨 Inspector’s Strategic Analysis (The 2FA Disaster):
Many believe enabling Two-Factor Authentication (2FA) is "Game Over" for hackers. However, modern hackers use Real-time Phishing to steal your 2FA code simultaneously. The solution? Use hardware security keys (like Yubikey) or dedicated apps like Microsoft Authenticator. Never trust SMS-based 2FA; it is defenseless against SIM Swapping attacks.

2. Info-stealer Malware: Thieves Walking in the Memory Layer
Your greatest enemies are no longer old-school viruses, but sophisticated malware families like Redline, Lumma, or StealC. These Info-stealers enter your system through deceptive means:
- Session Token Hijacking: Upon execution, these tools steal your browser cookies. This allows a hacker to enter your Steam or Discord account without a password and without a 2FA code, because the browser thinks your session is still valid.
- Browser-in-the-Browser (BitB) Attacks: The hacker designs a fake Steam login pop-up that appears to have the correct URL (steamcommunity.com) in the address bar, but is actually a graphical overlay on the hacker's site.
- Kernel-Level Keyloggers: Advanced malware that sends every keystroke to the hacker’s server before Windows even finishes processing the input.
3. Layer Three: Advanced Social Engineering; When "Trust" is Hacked

In 2026, hackers are psychologists as much as they are coders. They know how to exploit your emotions—fear, greed, or the desire to help a friend. Discord is the primary minefield for these cognitive attacks.
- The "Accidental Report" Scenario: Someone messages you: "Hey, I accidentally reported your account for a fraudulent trade, and Steam Support says you’ll be banned if you don't talk to them!" They then direct you to a fake "Steam Admin" on Discord to drain your data.
- Startup Game Testing: A hacker asks you to test a new "indie game" they are developing. The file they send is actually a Remote Access Trojan (RAT), giving them total control over your system.
4. Layer Four: Network Debugging; Defending at the Hardware Level
If a hacker cannot get into your account, they will try to kick you out of the game. DDoS attacks and IP leaks through old P2P protocols in certain games remain a massive security hole.

🛠️ Technical Insight (Network Hygiene):
Always use encrypted DNS (DoH) to prevent DNS Poisoning. If you are a competitive gamer, invest in a dedicated router with an SPI Firewall. This masks your real IP from automated scanners and neutralizes DDoS attacks at the modem layer.
5. Layer Five: OS Hardening; Securing the Core
To make the fortress truly impenetrable, you must debug the Operating System itself. The Inspector emphasizes these critical steps:
- Core Isolation (Memory Integrity): Ensure this is enabled in Windows 11 to prevent malicious code injection into the system's secure memory.
- UAC at Maximum: Set User Account Control to the highest level. If a file asks for admin rights without a clear reason, it is likely a payload attempting to escalate privileges.
- Offline Password Managers: Using managers that store databases locally (like KeePassXC) protects you even if a password manager company’s servers are breached.
📊 The Tekin Verdict
My fellow gamer, at the end of this deep autopsy, you must accept a cold truth: hackers are always one step ahead of software, but they cannot defeat a "debugged mind." Real security is not a collection of tools; it is a "Digital Lifestyle."
When you avoid cracked games, suspicious cheats, and tempting links, you activate the most powerful firewall in the world within your own brain. Your account represents years of memories and effort—don't open the gates for a free skin or a suspicious shortcut. Tekin Garage is here to help you protect your digital empire. Stay vigilant, keep your systems hardened, and always play in the safe zone!
